The zero trust security methodology addresses this challenge by shrinking the focus from one large security perimeter and instead creating smaller “micro-perimeters” around each individual resource that needs defending. It’s called zero trust because it follows the principle of “never trust, always verify.” That means each user and device needs to verify its identity and prove its trustworthiness before it can penetrate the micro-perimeter. So, for example, if a cybercriminal uses stolen credentials to log into the enterprise network, they have to pass through many different security checkpoints to see or access any sensitive resources, which increases the likelihood they’ll get caught before excessive damage is done.
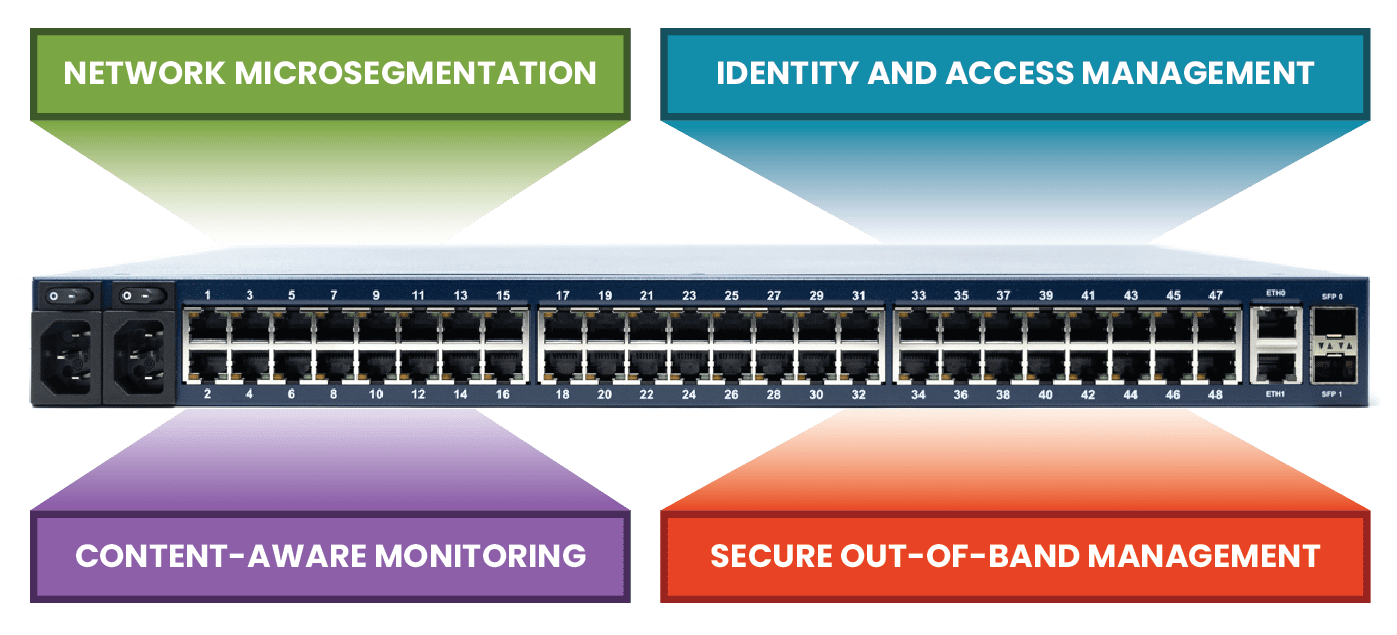
One way to implement micro-perimeters and apply zero trust security policies is with a device called a zero trust gateway. This post discusses the technologies that make up a zero trust gateway and explains how they work together to defend enterprise networks.
What is a zero trust gateway?
A zero trust gateway is a device that sits at the edge of the network – or at the top of the rack – and applies zero trust security policies and controls to traffic flowing in either direction. The gateway can be a dedicated security appliance, but it’s often more cost- and space-effective to use a multi-functional device that combines security, networking, and infrastructure management in a single box.
To see an example of a vendor-neutral zero trust gateway at work, request a demo of the Nodegrid solution from ZPE Systems.
Network micro-segmentation
A zero trust micro-perimeter is made up of granular access control policies and security controls that are custom-tailored to the specific vulnerabilities and requirements of resources they’re defending. For example, an on-premises database containing sensitive financial records needs different policies than a cloud-based application that doesn’t process any personal information. To implement micro-perimeters, resources first need to be logically organized based on their sensitivity level, who needs access to them, and what their interdependencies are.
Network micro-segmentation is used to separate resources based on these criteria so that micro-perimeters can then be applied. For a device to be considered a zero trust gateway, it must support VLAN micro-segmentation and be able to apply access control rules consistently across all micro-segments.
Identity and access management
In a zero trust architecture, user and device permissions should be limited to only what’s necessary to perform their job role. For example, an HR account used to manage employee records shouldn’t have access to customer financial data, and vice versa. Access policies should be specific to individual micro-segments and resources and need to be applied to all users and devices consistently, no matter where they’re logging in from. That means a remote user should follow the same authentication steps and have the same permissions as they would if they logged in at the office.
For a large enterprise network, this is only achievable with a centralized identity and access management (IAM) solution. An IAM provides a single platform from which to create, manage, and apply security policies. A zero trust IAM also enables best practices like single sign-on (SSO) and two-factor authentication (2FA).
A zero trust gateway needs to integrate with your chosen IAM provider to ensure that policies are applied to both production traffic and management traffic. Some vendor-neutral gateway solutions can even directly host and run third-party IAM solutions, providing a more integrated experience and saving rack space.
Context-aware monitoring
Many successful cyberattacks use stolen credentials gained through phishing schemes and other social engineering tactics. For example, Mailchimp was recently attacked by malicious actors using credentials stolen from employees through social engineering. It’s difficult to detect and contain such an attack because the criminal looks like an authorized user. However, careful monitoring often reveals suspicious behavior, such as logging in from an unusual IP address or time zone, making multiple access requests to areas of the network they don’t usually visit, or transferring abnormally large quantities of data.
User and entity behavior analytics, or UEBA, uses machine learning technology to monitor and analyze account activity on the enterprise network. UEBA creates a baseline of “normal” behavior for individual accounts so it can detect any anomalous activity. UEBA integrates with other security and monitoring solutions, such as IAM and firewalls, so it can compare data from various sources to make more informed decisions. This is one of the ways that zero trust security verifies the trustworthiness of accounts trying to access sensitive resources, making UEBA a critical component of zero trust gateways.
Secure out-of-band (OOB) management
Admins need a fast and reliable way to access remote infrastructure for management, troubleshooting, and recovery. For example, it’s common for a single data center management team to be responsible for customer equipment in multiple DCs distributed around the world for redundancy. These admins can’t physically go on-site every time a firmware update fails or a device loses its IP address. That’s why they rely on remote out-of-band (OOB) management; remote OOB management creates a separate network just for management traffic that doesn’t rely on the production LAN. Admins access the OOB network using a dedicated management device, like a jump box or a serial console server.
This management device is a tempting target for cybercriminals, as gaining control of that device will give them complete control over the connected infrastructure. One way to protect the OOB network is by using a zero trust gateway with integrated management ports. For example, the Nodegrid Net Services Router (NSR) is a modular zero trust gateway that can be customized to connect to any type of device that needs to be managed or secured. The NSR comes with gateway routing and switching capabilities, an embedded firewall, and hardware security features like secure boot and a self-encrypted disk. Nodegrid is also completely vendor-neutral, which means it can directly host or integrate with your choice of third-party security solutions, including next-generation firewalls (NGFWs) and zero trust technologies like identity and access management and UEBA.
The NSR is a modular, open platform upon which to build a fully customized zero trust gateway for large data center deployments. The Nodegrid product line from ZPE Systems also includes a variety of serial console solutions and integrated all-in-one gateway routers to support other use cases, such as edge computing sites, branches, and automated IoT deployments.
A zero trust gateway helps organizations implement micro-perimeters of specific policies and controls to defend sensitive data and other valuable resources. A vendor-neutral, integrated solution like the Nodegrid Serial Console Plus from ZPE Systems makes it possible to combine zero trust security with networking and management functionality to create a streamlined, cost-effective zero trust gateway deployment.
Ready to learn more about Zero Trust Gateway?
To learn more about deploying Nodegrid as a zero trust gateway in your enterprise, contact ZPE Systems today.
