Software-defined wide area networking, or SD-WAN, has made it possible to efficiently control highly distributed WAN architectures using software abstraction and automation. SD-WAN adoption is increasing, partially due to the rise in remote work during the pandemic, with experts predicting a compound annual growth rate (CAGR) of 26.2% between 2022 and 2028. However, while SD-WAN solves a lot of remote, edge, and branch networking problems, it also introduces security concerns that must be addressed. This definitive SD-WAN security checklist highlights the most important challenges and provides solutions for overcoming them.
The definitive SD-WAN security checklist
Keeping an SD-WAN architecture secure requires several features to be successful. It’s vital to consider this comprehensive list.
1. Frequent security patching
Outdated operating systems create a significant security risk. According to a 2016 Voke Media survey, about 80% of breaches or failed audits could have been prevented by patching outdated software or updating device configurations. An SD-WAN router with an outdated OS is more likely to have vulnerabilities, and the longer it goes unpatched, the more likely a hacker is to find and exploit those vulnerabilities.
However, SD-WAN architectures are often multi-vendor and highly distributed, making it challenging for administrators to monitor for vulnerabilities and stay on top of patch schedules. There are two primary ways to overcome this difficulty:
- Centralized SD-WAN management platforms provide a single pane of glass from which to monitor and update device software. The right platform is vendor-agnostic, so administrators can easily patch any and all vendor devices from one common interface.
- Automated patch management software helps keep OSes up to date by automatically applying new updates based on a predetermined schedule. Some solutions even perform automatic vulnerability scans or can monitor environments for missing patches and apply new updates that fall outside of the usual patch schedule.
Your ability to keep SD-WAN device software secure ultimately depends on the vendor’s patch schedule. Some providers are sluggish to patch known vulnerabilities in their software, either because they think they can keep said vulnerabilities a secret or because they don’t want to dedicate the time and resources needed to keep the OS up to date. That’s why you should look for SD-WAN hardware and software vendors who are transparent about vulnerabilities and who work diligently to release frequent patches and updates.
2. Zero Trust Provisioning
SD-WAN platforms are software-based, but they still require underlying networking hardware at each remote site for connecting to the enterprise network. Deploying this hardware can be difficult, especially when SD-WAN sites are in hard-to-reach locations such as offshore oil rigs, remote weather stations, or nations experiencing disasters or active conflicts. Often, organizations opt to pre-stage devices in their home office and then ship them to remote sites so they can avoid costly or dangerous travel.
Pre-staging creates a security risk because a pre-configured device could be intercepted by hackers and used to access the enterprise network. Zero Touch Provisioning (ZTP) reduces the need for pre-staging by deploying new device configurations over the network. ZTP-enabled devices provision themselves by using DHCP or TFTP to find and download configuration files, which means administrators can ship factory-default hardware that doesn’t contain any exploitable information about the enterprise network.
However, ZTP also introduces some additional security challenges. Once they’ve created the configuration file, administrators generally don’t monitor the entire automatic provisioning process, so there’s a chance that a mistake in the configuration file could create a security vulnerability that goes unnoticed. And, since one ZTP configuration file is usually applied to multiple devices, a potential security vulnerability could affect several systems or locations without anyone knowing. In addition, hackers could intercept the transmission of the configuration file over the network if the connection isn’t strongly encrypted.
These challenges are overcome with a secure ZTP solution that follows zero trust security principles. This type of solution is often referred to as “Zero Trust Provisioning,” and it includes hardware-based security like TPM, BIOS protection, encryption modules, and an onboard firewall which protects the software layer (secure boot) and management layer (two-factor authentication). In addition, the ideal Zero Trust Provisioning solution supports integrations with automated configuration management tools like Chef and Ansible which can be set up to test and monitor ZTP configurations for mistakes and security vulnerabilities.
Zero Trust Provisioning is a key part of the SD-WAN security checklist because it prevents branch networking hardware from being intercepted and used in a cyberattack. It also ensures that automatic provisioning occurs over a secure, encrypted network connection, and allows integration with configuration management tools to prevent errors from introducing additional vulnerabilities.
3. Secure out-of-band access
Many organizations use out-of-band (OOB) management to configure, control, and troubleshoot remote network infrastructure. OOB management uses a separate management plane, so resource-intensive network management and orchestration workflows don’t affect the performance or reliability of the production network. This may involve using a jump box to access an OOB network, which is an entirely separate management network architecture that runs parallel to the production network. However, a simpler solution is to use an OOB console server to achieve the same goal without the hassle of deploying a separate architecture.
OOB management improves the performance and reliability of production networks, and provides an alternative path to remote infrastructure (typically via cellular modem) in the event of an ISP outage or a network device failure. The issue with OOB management is that jump boxes and console servers are attractive targets to hackers. If a malicious actor manages to compromise the OOB network, they’ll gain complete control over the remote infrastructure.
To keep SD-WAN devices and other remote infrastructure secure, it’s best to use an OOB console server with advanced encryption for both the hardware and the management connections. In addition, the OOB solution should include Zero Trust features like MFA (multi-factor authentication) and RBAC (role-based access control). Just like the SD-WAN hardware, the OOB device(s) should run a fully patched OS and support Zero Trust Provisioning. For even greater protection, choose an OOB solution that supports integrations with third-party security solutions like next-generation firewalls (NGFW).
A secure out-of-band management solution gives network administrators 24/7 access to remote infrastructure on a dedicated, encrypted network connection using hardened OOB console server devices. This ensures that hackers can’t use the OOB network to hijack production infrastructure while also giving administrators the ability to quickly recover from outages, hardware failures, and cyberattacks.
4. Cloud-based security technology
As we’ve discussed above, it’s possible to run SD-WAN solutions on hardware with onboard firewall features. However, these basic firewalls often lack the advanced functionality needed to protect enterprise networks from sophisticated cyberattacks, which is why most organizations also use some form of stateful firewall or NGFW that resides in a central data center. This works well for a single, centralized enterprise network, but the addition of remote sites can create performance issues.
For the centralized firewall to inspect and protect SD-WAN traffic, that traffic must be backhauled through the central data center, even if the request is ultimately destined for the web. This inefficient routing causes bottlenecks, performance issues, and even dropped connections for on-premises and remote users alike. The obvious solution to this problem would be installing physical or virtual firewalls in each remote location, but this is expensive and disruptive and creates more management complexity for network administrators.
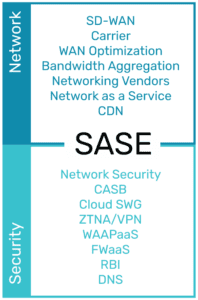
A better way to protect remote traffic while improving performance is through the use of cloud-based security solutions, such as Security Service Edge (SSE). SSE relies on SD-WAN’s intelligent routing capabilities to separate remote traffic that’s destined for web, cloud, and SaaS resources. This traffic bypasses the firewall and is instead routed through a cloud-based security stack, reducing the load on the enterprise network.
Ideally, the SD-WAN solution will tightly integrate with the SSE platform. This combination of SSE security with an SD-WAN on-ramp creates what’s known as SASE, or Secure Access Service Edge. This is most easily achieved using vendor-neutral branch networking platforms which can host or integrate with a wide variety of SD-WAN and SSE solutions. An integrated SASE architecture ensures comprehensive security while providing remote users and systems with fast, reliable access to cloud resources.
Nodegrid checks every box on your SD-WAN security checklist
Only one remote network management solution provides everything you need to keep your SD-WAN architecture secure: the Nodegrid platform from ZPE Systems. Nodegrid’s vendor-neutral routers, such as the 5-in-1 Hive SR branch gateway, can directly host or integrate with your chosen SD-WAN solution. Whether you enable SD-WAN with a Nodegrid device or by using ZPE Cloud’s SD-WAN application, you’ll get seamless access, centralized management, and state-of-the-art security.
1. Secure, up-to-date SD-WAN device OS
Nodegrid’s branch gateway routers run on the vendor-neutral, x86 Linux-based Nodegrid OS, which is constantly monitored for vulnerabilities and frequently patched to ensure security. Plus, with the ZPE Cloud orchestration platform, you can monitor and update all your SD-WAN devices from one convenient management portal—even if that hardware comes from another vendor.
2. Zero Trust Provisioning for branch networks
All Nodegrid devices support Zero Trust Provisioning, and they can extend this capability to any third-party devices managed by Nodegrid. That means administrators can securely configure all the multi-vendor devices in a remote branch network without the need for travel or pre-staging. Nodegrid ZTP is considered Zero Trust because it protects the hardware, software, and management layers with advanced security features like:
- Password-protected BIOS
- Current cryptographic modules
- SSO with SAML (Duo, Okta, Ping, and ADFS), MFA, and remote authentication
- Geofence perimeter crossing detection
- Onboard firewall, IPSec, and Fail2Ban intrusion protection
- Fine grain RBAC with strong password enforcement
Nodegrid also supports integrations with automated configuration management solutions like Ansible, Chef, and Puppet, so you can ensure every device is provisioned correctly.
3. Gen 3 secure out-of-band management
Nodegrid services routers provide reliable, Gen 3 OOB management access to any connected devices, including those from other vendors. This access is protected by a patched OS, onboard hardware security features, and current encryption modules. Plus, Nodegrid’s hardware and software can host or integrate with third-party security solutions like NGFWs for comprehensive OOB security.
4. An SD-WAN onramp to SSE
The Nodegrid branch networking solution provides the ideal SD-WAN on-ramp to leading Security Service Edge providers. That’s because Nodegrid is a completely open platform that can host or integrate with any SSE and SD-WAN offering to provide a single, unified SASE solution. This gives administrators complete control over every aspect of branch network management and SD-WAN security from one convenient portal, reducing complexity and improving your security posture at the same time.
Wondering how ZPE’s Nodegrid solution checks all the boxes on your SD-WAN security checklist?
Contact ZPE Systems today to learn more