ZPE Systems Introduces NSR 2U and NVIDIA Jetson Expansion Card, Combining AI Acceleration, Networking, and Infrastructure Resilience

Las Vegas, NV — June 1, 2026 – At Cisco Live 2026, ZPE Systems (a brand of Legrand) today announced the Nodegrid Net Services Router™ 2U (NSR 2U), a modular, next-generation x86 platform that consolidates routing, network services, and out-of-band (OOB) management into a single, centrally managed system for distributed and edge environments.
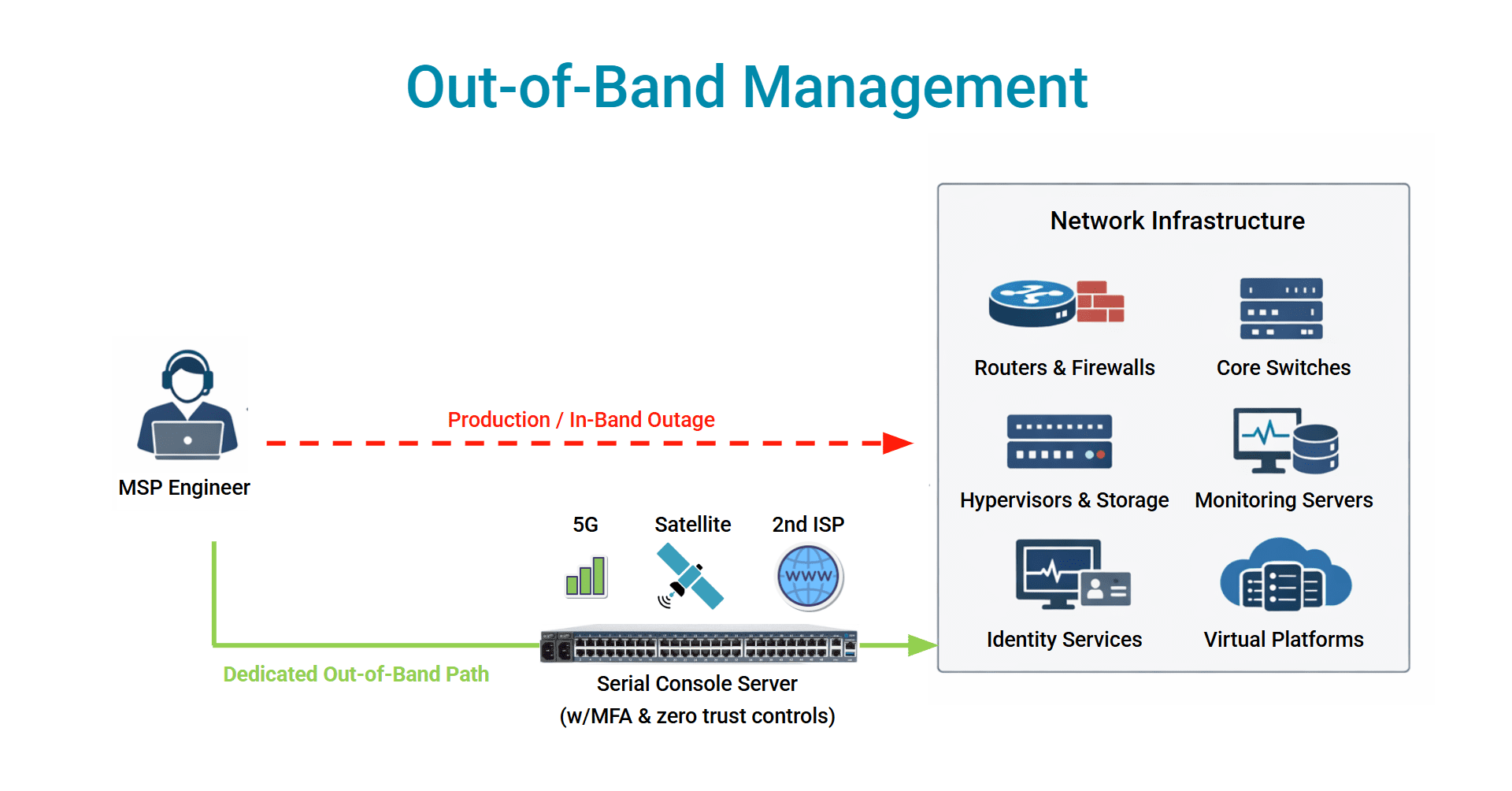
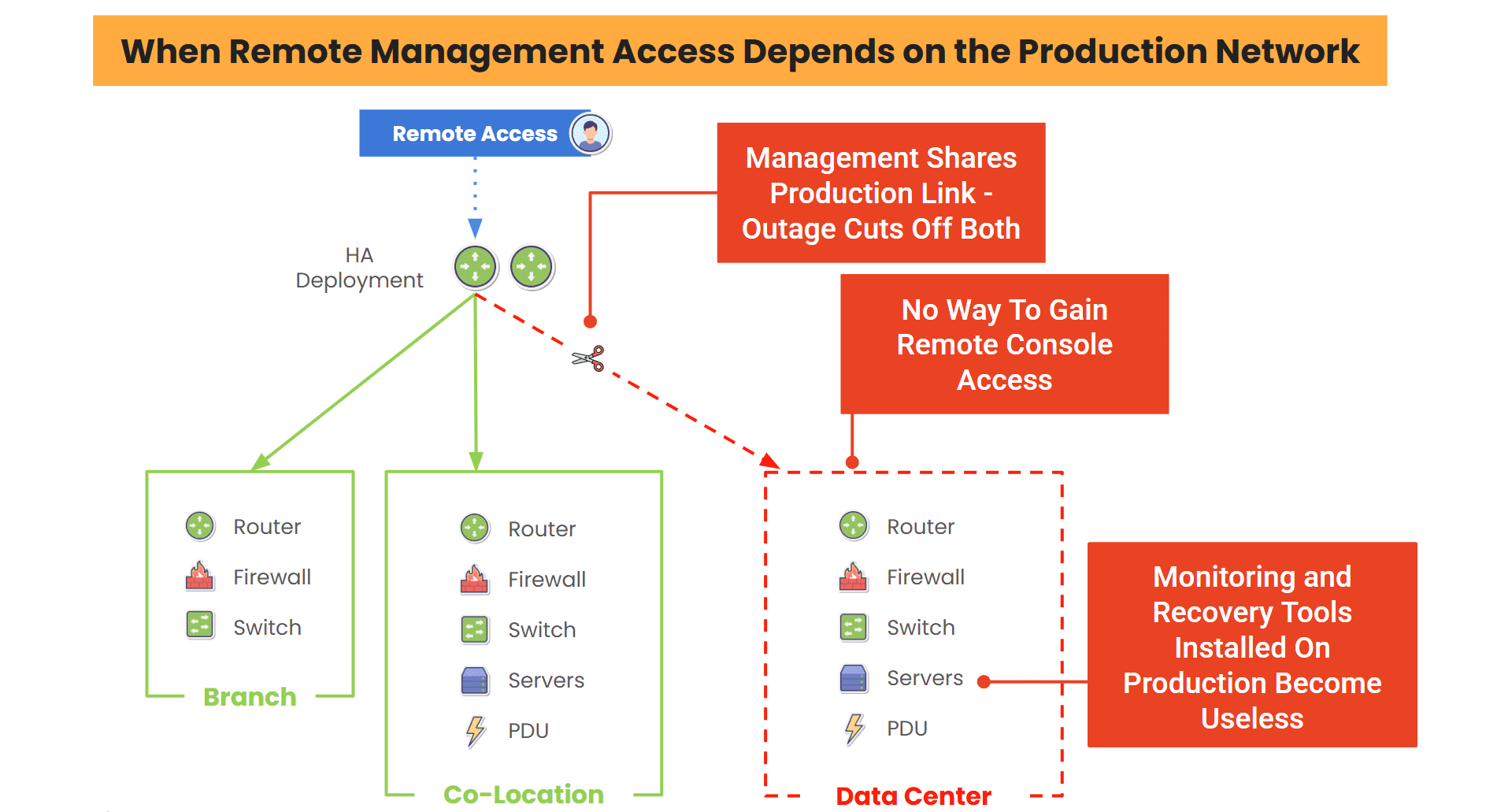
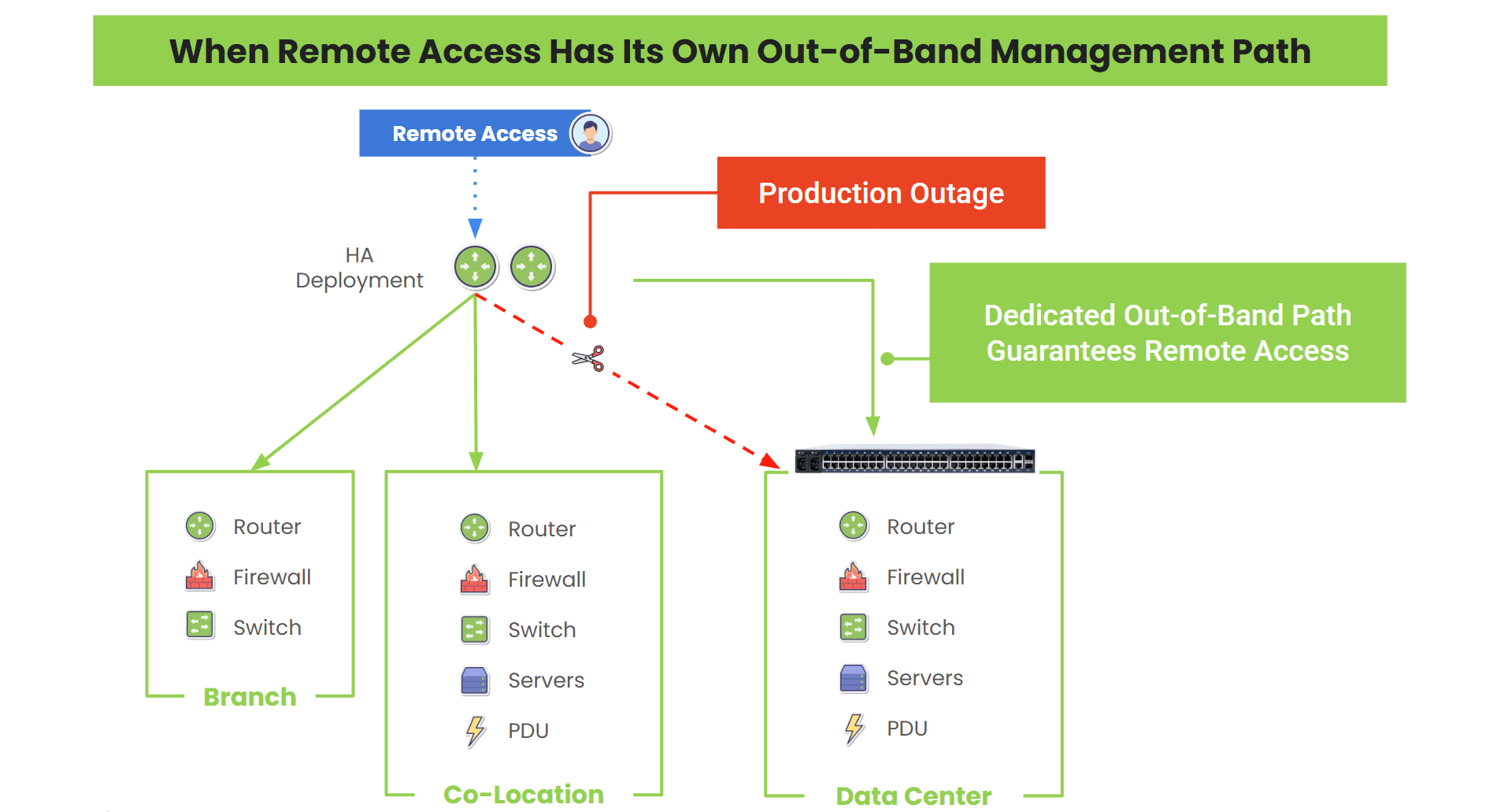
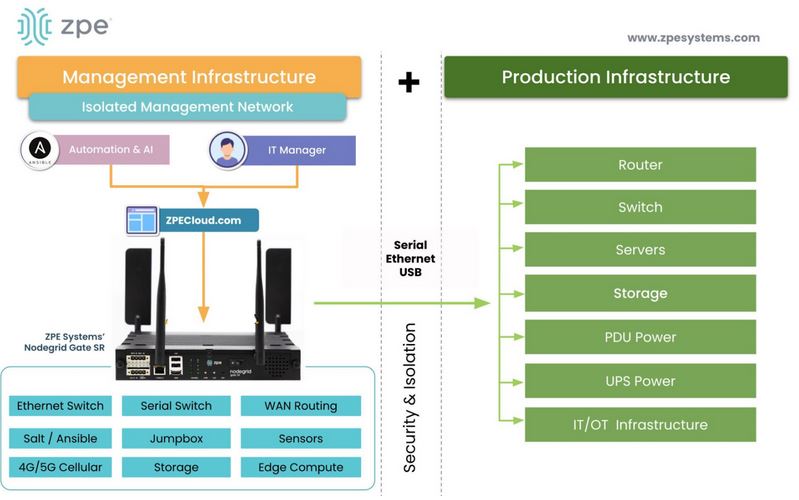
As organizations expand AI workloads across edge and distributed environments, infrastructure teams face growing operational complexity, rising downtime risks, and limited visibility during outages. The NSR 2U addresses these challenges by combining networking, AI acceleration, compute, and integrated out-of-band management into a single resilient platform.

Alongside the new platform, ZPE Systems is introducing the NVIDIA Jetson AI Expansion Card for NSR—backward compatible with both NSR and NSR 2U—enabling customers to run edge AI inference and acceleration directly on the device at the edge without adding external servers or operational complexity.
The NSR 2U represents a significant leap in performance, modularity, and serviceability, providing organizations with a future-ready foundation for secure, scalable, and automated infrastructure operations.
The combination of AI acceleration and integrated OOB management enables organizations to build infrastructure that can both detect issues intelligently, and also remain reachable and recoverable during failures. Setting a new industry standard, the solution is the first platform to combine networking, edge AI, compute, and recovery in one system, providing a resilient, AI-ready solution that keeps infrastructure running during primary network outages.
“Our customers are managing increasingly complex remote sites with minimal on-site staff and told us they needed a single platform that could do it all from anywhere. The NSR 2U is that platform — and with the NVIDIA Jetson Expansion Card, it brings AI-powered network operations to the edge,” said Vishal Gupta, Director of Product Management, ZPE Systems. “It’s the most capable Nodegrid appliance we’ve ever built, driven entirely by customer demand.”
A New Standard for Edge, Cloud, and Data Center Infrastructure
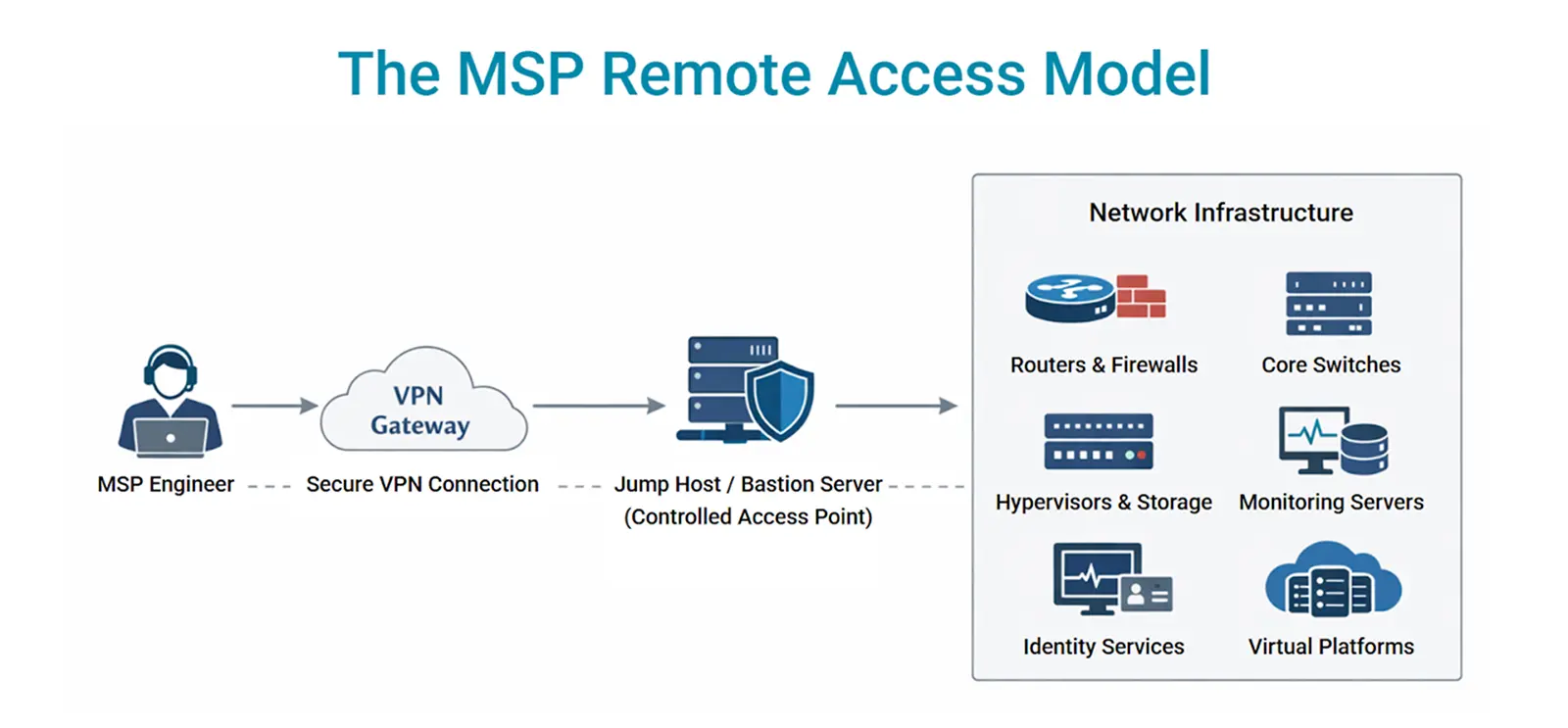
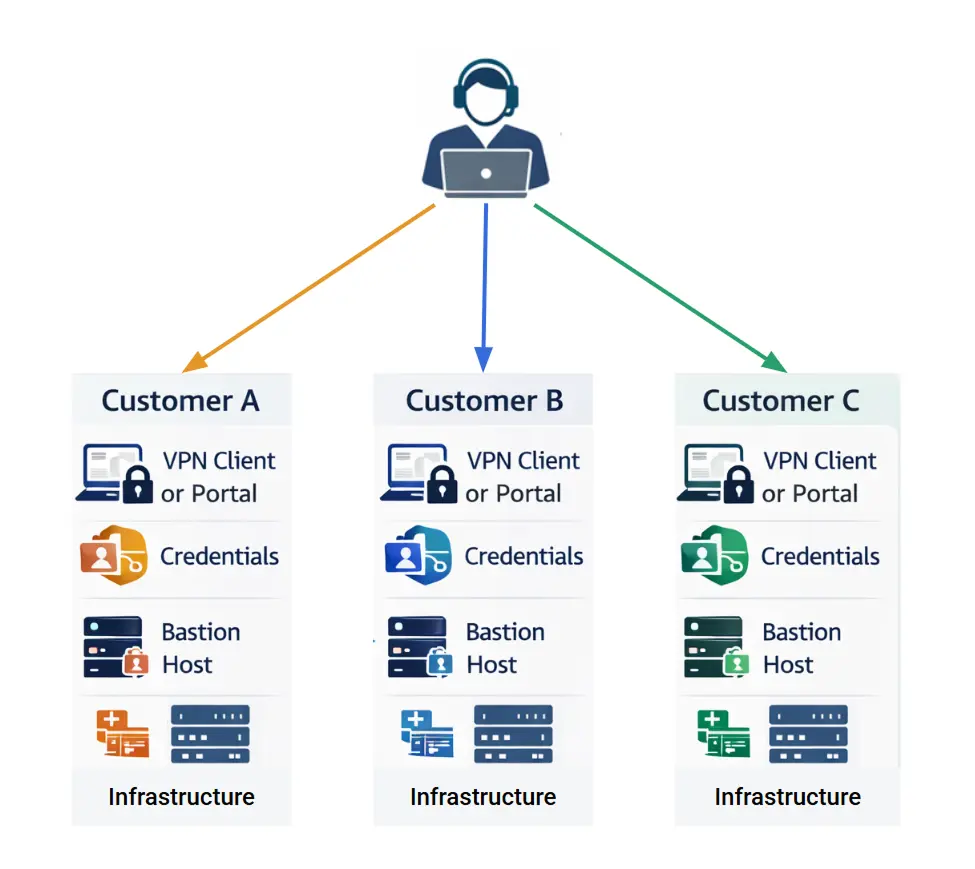
The NSR 2U is purpose-built to consolidate networking, compute, and management into a single platform capable of running diverse workloads across edge, cloud, and data center environments.
It supports a wide range of functions, including high-performance switching, security services, WAN optimization, containerized applications, and resilient out-of-band access, all within a unified system.
Its 2U architecture, combined with 10 expansion slots, upgraded compute, and a next-generation switching fabric, gives organizations the flexibility to build and scale infrastructure based on their exact requirements, without overprovisioning or deploying multiple appliances.
This makes the NSR 2U ideal for distributed enterprises, retail and remote locations, service providers, and converged infrastructure (CI) deployments.
AI at the Edge: Introducing the NVIDIA Jetson AI Expansion Card for NSR
The newly launched NVIDIA Jetson AI Expansion Card for NSR brings GPU‑powered intelligence directly into the Nodegrid ecosystem. Designed for both the NSR and NSR 2U platforms, this card enables customers to run AI/ML workloads where they matter most: close to data sources, users, and critical infrastructure.
This new module allows organizations to:
- Run real‑time inference for security analytics, anomaly detection, and predictive maintenance
- Deploy AI‑driven automation for network optimization and event correlation
- Process video, sensor, and telemetry data locally to reduce cloud dependency
- Consolidate AI, networking, and OOB management into a single, compact platform
By integrating NVIDIA Jetson into the NSR architecture, ZPE Systems eliminates the need for separate edge AI devices, reducing cost, complexity, and power consumption while enabling resilient, AI-driven infrastructure operations that remain manageable and recoverable even during outages.
With the NSR 2U and NVIDIA Jetson, ZPE Systems is redefining infrastructure operations for the AI era by bringing networking, intelligence, and resilience together into a single platform.
Explore the NSR 2U and NVIDIA Jetson Card by visiting the links below. Explore product specs, download the data sheet, and set up a demo to get hands-on with these new products!