ZPE Systems announces Nodegrid Data Lake, app marketplace, and sensors to help organizations uncover valuable data for edge operations
Enterprises in telco, content delivery, manufacturing, and other industries can benefit from Nodegrid Data Lake. This application gathers previously uncollected data points to give network admins and engineers visibility into key performance indicators (KPIs). Nodegrid Data Lake helps inspect and visualize data points for:
- Infrastructure components, such as power, cooling, relay, dry contact
- Environmental conditions, such as temperature, humidity, air flow
- System utilization, such as disk usage, processes, memory
- User experience applications, such as Office365, Zoom, point of sale
- Security, such as system logs, data logs, GPS data
- Networking, such as data traffic, application profiling, antenna/tower traffic
- Previously hidden server and switch logs from IPMI and RS232 serial console
Gartner considers Nodegrid Data Lake a killer app, as it’s indispensable to maximizing business continuity and avoiding downtime.
ZPE Cloud’s additional applications help enterprises and resellers gain further insights and convenience. These applications include:
- Extended Storage — Save time with centralized file management and add disk space via the cloud
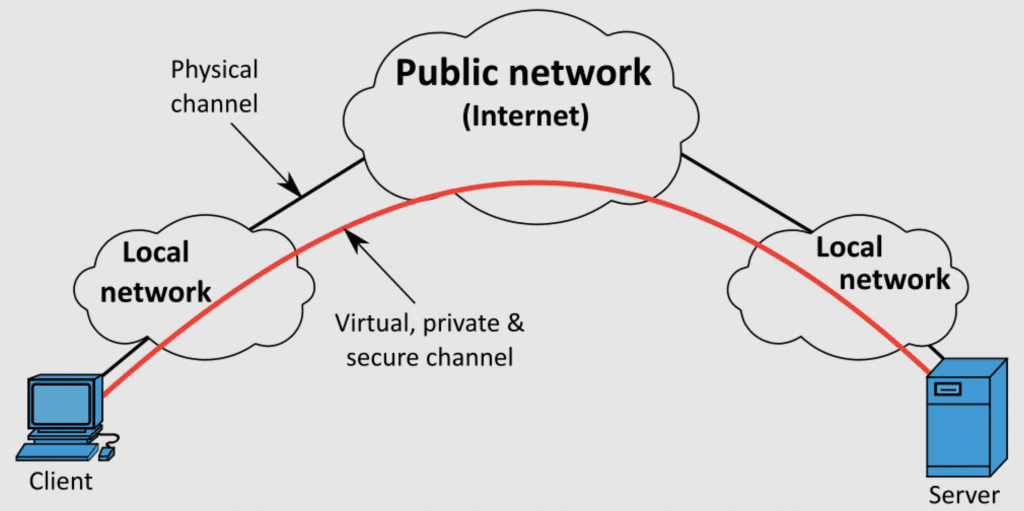
- Generic Forwarder — Secure distributed users with software-defined perimeter gateways on-prem or cloud-delivered
- Reports — Drive smart decision making with comprehensive reports on device availability and other metrics
- Palo Alto Prisma Access — Easily manage Palo Alto security solutions using centralized access
- ZPE Cloud mobile — Never lose sight of network performance using the ZPE Cloud mobile app, available free on App Store and Google Play
These applications begin an extended product roadmap designed to optimize the configuration, access, and management capabilities offered via ZPE Cloud.
ZPE Systems also launches USB-type environmental sensors, to help ensure optimal utilization of critical physical infrastructure components. These sensors can be managed independently via Nodegrid devices, or via Nodegrid Data Lake for complex event processing. Nodegrid sensors support alert triggers and tracking, and integrate seamlessly with ZPE Cloud’s management interface. Available sensors include:
- Temperature and humidity
- Airflow and temperature
- Smoke
- Particulate
- GPIO
- Relay
- Proximity
- Beacon (no alarm)
- Beacon (with alarm)
- Door lock with RFID tag
“IT staff struggle with downtime, yet their infrastructure generates so much valuable data that goes to waste,” says Arnaldo Zimmermann, CEO and Cofounder of ZPE Systems. “Our apps and sensors help capture this information. They can use it to prevent device failures, adjust cooling systems, or pinpoint why their Zoom app is suddenly lagging, for example.”
Nodegrid Data Lake and ZPE Cloud apps are now available. Get a free 90-day trial by visiting the ZPE Cloud Apps page.
Nodegrid sensors are also available. Learn more on the Nodegrid Environmental Sensors page.
About ZPE Systems, Inc.
ZPE Systems frees enterprises from today’s networking challenges.
Nodegrid’s Intel-based serial consoles & modular services routers deliver power to datacenter & branch applications, while the Linux-based Nodegrid OS replaces vendor lock-in with limitless flexibility. With ZPE Cloud for fast & secure provisioning, this platform streamlines networking using virtualization, prevents downtime using automation, and offers convenience via remote management capabilities.
Intel-based serial consoles & modular services routers deliver unparalleled power to datacenter & branch applications, while the Linux-based Nodegrid OS replaces vendor lock-in with limitless flexibility. With ZPE Cloud for fast & secure provisioning, it’s the only networking platform to streamline the stack using virtualization, prevent downtime using automation, and offer convenience using in-depth remote management capabilities.
ZPE collaborates with best-in-class technology partners, to add value by integrating with SD-WAN, firewall, IoT, and other solutions. The world’s top companies trust ZPE Systems to provide advanced out-of-band management, Secure Access Service Edge (SASE) platforms, and SD-Branch networking.
Top companies trust ZPE Systems to provide advanced out-of-band management, Secure Access Service Edge (SASE) platforms, and SD-Branch networking.
ZPE Systems is based in Fremont, California with offices worldwide. Visit ZPE Systems website at
www.zpesystems.com.