What Are the Key Zero Trust Security Principles?

Perimeter-based security is no longer sufficient for today’s enterprise network. You may even struggle to define your network perimeter anymore, mainly if you use cloud infrastructure, have remote data centers and branch offices, or rely on “Internet of Things” (IoT) devices in the field. Zero trust security addresses the weaknesses in a perimeter-based strategy by focusing on protecting and securing your users, devices, and services wherever they may be located.
The methodology of zero trust security is “never trust, always verify.” That means you operate under the assumption that no network entities should be trusted, whether they’re inside or outside the enterprise network. To implement this strategy, you must understand the key zero trust security principles and how they work together to protect your enterprise.
What are the key zero trust security principles?
For a successful zero trust security implementation, your enterprise should follow these four key principles:
1. Define your protect surface, not your perimeter
The first key principle of zero trust security involves shrinking your focus from the network perimeter to the individual systems and services you need to protect.
Traditional perimeter-based security strategies require you to identify and defend an attack surface—the sum of all the potential vulnerabilities and access points that a hacker could use to breach your network. You then need to create and maintain a perimeter around your entire network, with security policies and controls that account for every possible weakness.
However, as your enterprise networks expand to include remote data centers, public cloud platforms, work-from-home employees, and other complications, your attack surface grows more complex. How do you create and defend a perimeter that large, and how can you possibly account for every network vulnerability with one set of security policies and controls? With zero trust security, you don’t have to.
Instead, you need to define your protect surface in a zero trust security strategy—each specific network entity you need to protect from an attack. A protect surface should fall under one of these four categories, known by the acronym DAAS:
- Data: The sensitive, proprietary, or legally regulated data that you need to keep private. You should identify and classify your data based on its value (to your company and hackers) and relative sensitivity so you can implement the right security policies and controls to protect it. The best way to do so is with data discovery tools that automatically index, classify, and organize data according to your requirements.
- Applications: The applications that introduce security vulnerabilities to your network, contain proprietary code, or process sensitive data. You also need to protect and map all application interdependencies (e.g., databases, enterprise servers, third-party integrations, etc.) to ensure your security controls don’t break anything or leave any weaknesses unaccounted for. Automation is also recommended for this task—you can use application dependency mapping software to identify and trace interdependencies on your network.
- Assets: The devices that connect to your enterprise network. In addition to inventorying your users’ laptops, cell phones, and other desktop devices, you also need details on every point-of-sale terminal, security camera, and IoT device. No matter how small or inconsequential a device is, if it touches your network, you need to know what it is so you can protect it. You’ll also need device details such as the serial number and firmware version to verify its identity with your zero trust security controls. You should employ an automated device discovery tool to find all the devices on your network and collect the necessary information.
- Services: The business-critical services that a hacker could take down to cripple your networks, such as DNS, DHCP, and Active Directory. Hackers can also use these services to gain access to other areas of your network with more valuable data—for example; a recent report found that 79% of companies experienced DNS attacks in 2019. If you’re following network management best practices, you should already monitor these services, which makes this step easier. Otherwise, you need to invest in and implement a comprehensive infrastructure and network monitoring solution. You simply can’t adopt a zero trust security strategy without complete visibility on your entire enterprise infrastructure.
Defining your protect surface is the first principle of zero trust security because you simply cannot apply any of the following components without this information. Once you’ve done that, you can move on to principle No. 2.
2. Apply micro-segmentation and micro-perimeters
The second principle of zero trust security is segmenting your network as much as possible, and then you can apply highly specific security policies and controls in your micro-perimeters.
After you’ve defined your DAAS, mapped interdependencies, and identified the individual vulnerabilities and access points that need to be protected, you can determine how you’ll segment your network. Look at which items can be logically sorted together based on who or what needs access to them, which security controls are required to protect them, and how they interact with other resources inside and outside your enterprise. Then, you’ll create your micro-perimeters around each network segment.
The goal is to create policies and controls that are highly precise to the DAAS you’re protecting. You should use the principle of least privilege (PoLP) to inform your policies. PoLP states that network entities should only receive the permissions necessary to perform their function. This ensures that a compromised account can only access limited resources on your network, which reduces the amount of potential damage a hacker could do to your network.
You’ll need advanced firewalling technology to create your micro-segments and micro-perimeters and to enforce your policies. For example, you could use a firewall as a service (FWaaS) solution that takes all the next-generation firewall functionality and makes it available as a cloud-based software platform. You can use FWaaS to manage your zero trust micro-perimeters across your entire enterprise network, including in the cloud and remote data centers.
These first principles focus on how to implement a zero trust security strategy. Next, we’ll look at the principles involved in actively using a zero trust security strategy in your enterprise.
3. Assess trust dynamically and consistently
As previously stated, the foundation of zero trust is “never trust, always verify.” This means any time an account wants to access a network resource, you need to verify their identity and trustworthiness first. You must assess their reliability dynamically based on the context of the situation. Is this a standard time for this user to be online? Are they in a geographic location that makes sense in this situation? Has this account been involved in any suspicious behavior elsewhere on your network? You need to consistently apply the same criteria every time this account tries to access a network resource, whether they’re in the home office or traveling abroad.
To apply this level of scrutiny to all your network entities, you’ll likely need an identity and access management (IAM) solution that incorporates user and entity behavior analytics (UEBA). UEBA establishes a baseline for the expected behavior of users and network entities, so it can then spot unusual or risky activity and report it. Your zero trust IAM and firewall solutions can then use that information to assess the trustworthiness of the entity requesting access.
4. Monitor and optimize constantly
As mentioned above, you can’t implement zero trust security without complete visibility on every part of your enterprise network. You need monitoring tools to discover your DAAS, track the traffic flow between micro-perimeters, and verify that security policies and controls are being applied correctly, for example.
A zero trust security architecture can be very challenging to monitor because networks are so distributed and highly segmented. To ensure full visibility on every micro-segment, you need a monitoring solution that employs automation and machine learning to ease the burden on your engineers. For example, security orchestration, automation, and response (SOAR) solutions can detect security incidents, identify root causes, and apply or recommend remediations without any human intervention.
Some unified zero trust security solutions include monitoring functionality or recommend integrations that address these challenges. However, one of the benefits of zero trust security for enterprises is that you can often use your existing tools and infrastructure without needing an expensive upgrade. So, if you’re already using SIEM (security information and event management) or another automated network management solution, you can likely achieve the level of visibility you need.
Lastly, you should always look for opportunities to optimize your zero trust security strategy. With your monitoring logs and analyses, you should be able to spot any weaknesses or other issues with your micro-perimeters, policies, and controls. It is also necessary to keep building out your zero trust architecture as you add or change applications, infrastructure, and workloads. Additionally, you should keep an eye out for ways to smooth and optimize the process of creating new network segments and micro-perimeters.
Applying key zero trust security principles in your enterprise
Though zero trust security is powerful enough to protect modern enterprise networks from cyberthreats, the strategy can be broken down into four key principles. Abandon the idea of a large network perimeter and focus instead on identifying the individual data, applications, assets, and services you must protect. Larger enterprises need a heavily segmented zero trust architecture, with precise security policies and controls creating a micro-perimeter around each segment. With these policies and controls, you must dynamically and consistently assess the trustworthiness of every network entity and constantly monitor and optimize your zero trust network.
Applying these key zero trust security principles in your enterprise is much easier with a unified platform that integrates all your tools, features, and controls behind one pane of glass, like ZPE Cloud. Not only does ZPE Cloud provide vendor-neutral integrations with zero trust tools like Okta and Duo, but you can also use it to manage your entire infrastructure whether on-prem or in the cloud. ZPE Systems also offers the Nodegrid line of network management solutions for remote out-of-band network management, SD-WAN, and secure access service edge (SASE) to complement your zero trust security architecture.
Learn more about how ZPE Systems can help you apply zero trust security principles in your enterprise.
Book a free demo or contact us anytime.


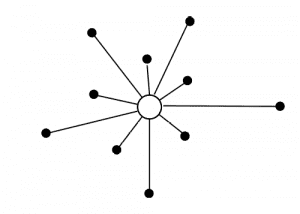 A centralized network is built around a single, central server that handles all major management and data processing functions. Other types of servers may connect to this master server and manage other specific functions, but those other servers cannot work independently of the central server.
A centralized network is built around a single, central server that handles all major management and data processing functions. Other types of servers may connect to this master server and manage other specific functions, but those other servers cannot work independently of the central server.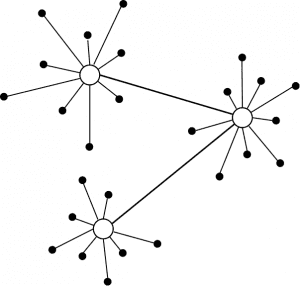 A decentralized network architecture uses multiple servers in place of a single centralized server. Each of these servers can act as an independent master server, with the necessary workloads distributed across them for load balancing. If one server goes down, another server can take over its load to minimize network interruption.
A decentralized network architecture uses multiple servers in place of a single centralized server. Each of these servers can act as an independent master server, with the necessary workloads distributed across them for load balancing. If one server goes down, another server can take over its load to minimize network interruption.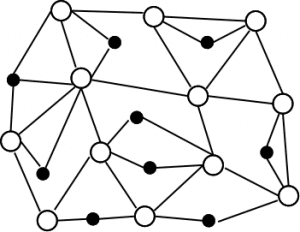 In a distributed network, all network services and coordination tasks are split evenly among many equal servers across the entire enterprise network.
In a distributed network, all network services and coordination tasks are split evenly among many equal servers across the entire enterprise network.


