
As inflation rises, new business declines, and another COVID-19 surge looms on the horizon, many organizations are bracing for a recession. CIOs and IT managers are having to do more with less—less staff, less budget for upgrades and repairs, and less access to on-site infrastructure. Despite these restrictions, they still need to ensure the 24/7 availability and optimal performance of enterprise network resources as any amount of downtime could severely impact business revenue.
The ability to continue providing digital services in less-than-ideal situations is known as network resiliency. Network automation is a key tool for ensuring resiliency during staffing shortages and lockdowns, and a network automation framework provides the tools and methodologies needed to create a fully-automated network infrastructure.
The four building blocks of a resilient network automation framework include:
- IT/OT production infrastructure
- Automation infrastructure
- Orchestration infrastructure
- AIOps
We’ve previously discussed the role of IT/OT production infrastructure in network automation and how an IT/OT convergence strategy accelerates network automation. In this post, we’ll describe the automation infrastructure components that enable end-to-end network automation. Future blogs will explain how the orchestration infrastructure layer and AIOps layer build upon these components to ensure business resiliency.
What is automation infrastructure?
Automation infrastructure is composed of all the hardware and software solutions that enable automation to occur. These solutions target the IT and OT production infrastructure and automate some or all of their workflows.
Key automation infrastructure components
There are a variety of hardware and software solutions that provide automation capabilities for specific workflows, use cases, and deployment models. As part of a resilient network automation framework, the most important automation infrastructure components include:
Gen 3 OOB serial consoles
Serial consoles are typically installed in data centers and used to manage other devices over a serial cable connection. They create an out-of-band management (OOBM) network that’s dedicated to troubleshooting, management, and orchestration traffic, and which is accessible via a secondary internet connection (often using cellular). This secondary connection ensures administrators always have remote management access to critical data center infrastructure even when the primary ISP, WAN link, or production LAN goes down. That means businesses can recover from outages faster and without dispatching expensive truck rolls.
The latest generation of serial consoles, Gen 3, gives administrators the ability to automate workflows on all data center infrastructure. Gen 3 serial consoles are vendor-neutral, which means they can extend their automated management capabilities to any vendor’s device. That vendor neutrality also means that Gen 3 serial consoles support custom scripts and third-party automation tools in addition to whatever automation capabilities are built-in.
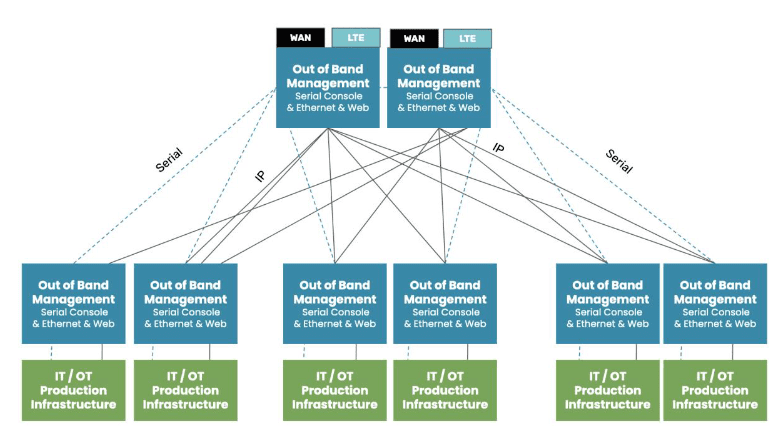
For peak resiliency, data center deployments should follow a two-tier OOB architecture. That means each rack of IT/OT production infrastructure should connect to its own Gen 3 serial console, which provides OOB management access and automation. These top-of-rack serial consoles should then connect to an OOB appliance in the middle or end of the row. This ensures OOBM access for the top-of-rack appliances and creates an additional layer of redundancy and resiliency.
- → Integration support for third-party security solutions like next-generation firewalls (NGFWs), security service edge (SSE), and SAML 2.0
- → An up-to-date operating system (OS) kernel that’s frequently patched by the vendor when vulnerabilities are identified
- → Onboard firewall functionality to inspect traffic on both the OOB network and the production network
- → Hardware security features like encrypted boot sequences and BIOS protection to prevent unauthorized access on stolen serial consoles
Gen 3 OOB serial consoles are the automation infrastructure components that enable automation and resiliency for data center deployments at the core of enterprise networks.
SD-WAN gateway routers
A gateway router is used to connect a LAN infrastructure to the internet and the enterprise WAN architecture. As part of a resilient network automation framework, all gateway routers should support SD-WAN (software-defined wide area networking).
SD-WAN separates the control and management processes from underlying WAN hardware and virtualizes them as software. SD-WAN uses features like application awareness and guaranteed minimum bandwidth to automatically optimize network performance. An SD-WAN solution can also use automatic load balancing and failover to ensure continuous availability in the event of a localized failure or data center outage.
SD-WAN is usually a cloud-based service that delivers centralized management and orchestration of automated workflows. This service runs on top of the gateway routers deployed at each site.
An SD-WAN gateway router is a key automation infrastructure component for the main office, data center, branch, and edge deployments because it enables automated WAN management and orchestration. An all-in-one cloud-managed gateway router is particularly useful for OT automation in remote facilities like warehouses and factories because it provides SD-WAN capabilities, OOBM, and routing in one multi-function device.
Monitoring, visibility, and analytics
Monitoring and visibility solutions give administrators virtual eyes and ears on remote network infrastructure. As part of a resilient network automation framework, a visibility solution should be vendor neutral so it can dig its probes into any device in a mixed vendor environment. It should also include environmental monitoring sensors that collect data on conditions in the rack.
Device monitoring and environmental sensors give administrators the ability to detect potential issues and respond quickly to prevent outages. Monitoring and visibility solutions also collect valuable data that can feed into the AIOps building block of the network automation framework.
Infrastructure as Code
Infrastructure as Code, or IaC, uses software abstraction to decouple infrastructure configurations from the underlying hardware. Configurations are written as scripts or definition files that automatically provision virtual machines (VMs), containers, or software-defined networking (SDN) devices. An IaC definition file can be deployed repeatedly, which means many identical resources can be spun up quickly while ensuring consistent configurations. An IaC config can also undergo automatic security testing before it’s deployed to any devices to prevent vulnerabilities from affecting production.
Another important aspect of IaC is automatic configuration management. Configuration management solutions like RedHat Ansible allow administrators to define the desired state of a system or network resource. The configuration management tool continuously monitors the resource to detect unauthorized changes, which might be made by a careless sysadmin or could be a sign of a malware infection. As soon as the change is detected, the configuration management solution uses a programmatic playbook to take whatever actions are needed to restore the system to its proper state.
IaC helps ensure network resiliency by reducing human error in device configurations and updates, as well as by enabling the use of pre-production automated security vulnerability scanning and configuration management. Infrastructure as Code also facilitates another key automation infrastructure component—immutable infrastructure.
Immutable infrastructure
In-place system and device updates are a common cause of hangs or failures which can be challenging to resolve remotely. Immutable infrastructure resolves this problem by eliminating updates and configuration changes altogether. Immutable infrastructure refers to virtual systems and network resources that are never changed in place. If an immutable resource has an issue or vulnerability, or if its OS is out of date, an entirely new resource is spun up and the old one is simply deleted.
IaC is an immutable infrastructure best practice because it gives administrators the ability to provision many devices very quickly and with identical configurations. Immutable infrastructure is secure, easy to deploy, and resilient to failure, making it an important part of the network automation framework.
Why Nodegrid is a key automation infrastructure component
The automation infrastructure building block of the network automation framework relies on vendor-neutral OOBM devices like gateway routers and Gen 3 serial consoles that extend automation to converged IT/OT production infrastructure. These devices must also support monitoring and visibility solutions, Infrastructure as Code with configuration management, and immutable infrastructure.
For example, the Nodegrid platform from ZPE Systems includes OOB management hardware for a variety of data centers, branch, and edge deployments. Nodegrid serial consoles, such as the NSCP, can dig their hooks into any device in your data center to enable end-to-end network automation. A Nodegrid Gen 3 OOB serial console can even extend IaC and immutable practices to legacy devices to ensure resiliency without expensive forklift upgrades.
Nodegrid services routers, such as the Mini SR, are compact edge gateways that deliver SD-WAN support, OOBM, and cloud management capabilities to IT/OT infrastructure in smaller branch office and edge data center deployments. Nodegrid SRs can help you consolidate an entire rack of branch infrastructure into a single device to reduce management complexity, CapEx, and OpEx.
Nodegrid out-of-band is delivered via WiFi, Ethernet, or 5G/4G LTE to ensure administrators have fast and reliable access to remote infrastructure. All Nodegrid OOB devices are protected by robust hardware security features like BIOS protection, UEFI Secure Boot, geofencing, disk encryption, and TPM 2.0. Plus, Nodegrid supports integrations with Zero Trust Security solutions like identity and access management (IAM) and SAML 2.0, as well as providing an on-ramp to SSE.
Nodegrid serial consoles and services routers also include interfaces for environmental monitoring sensors to collect crucial data about conditions in your rack. These sensors, as well as any other connected devices, can all be observed and managed from a single, centralized monitoring and reporting platform.
What makes Nodegrid a crucial element of automation infrastructure is its ability to directly host Infrastructure as Code and automated configuration solutions, including Ansible, Chef, Puppet, SaltStack, Monit, and Docker. Nodegrid appliances can then extend the capabilities of the IaC solution to any of the modern, legacy, and mixed-vendor devices it manages.
ZPE’s Network Automation Blueprint
Automation infrastructure works together with IT/OT production infrastructure, orchestration, and AIOps to ensure network resiliency during uncertain times. The Network Automation Blueprint from ZPE Systems provides a reference architecture for achieving Gartner’s definition of hyperautomation as well as meeting the Open Networking User Group (ONUG) Orchestration and Automation recommendations.
In future blog posts, we’ll discuss the remaining two building blocks of the Network Automation Blueprint in depth. In the meantime, you can read about IT/OT production infrastructure or click here to get a sneak peek of the blueprint, which includes a 10-step checklist to get started with automation now.
Want to learn more about key automation infrastructure?
To learn more about Nodegrid as a key automation infrastructure component, contact ZPE Systems today.
