Top Security Service Edge Use Cases & Benefits for Enterprises

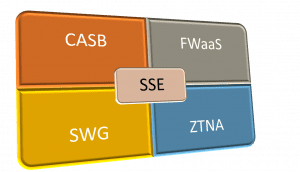
Security service edge (SSE) is an emerging network security model, first announced by Gartner in their 2021 Hype Cycle, that stems from the need to retool the industry’s thinking about SASE (secure access service edge). SSE protects your network edge by combining cloud-based security technologies, including:
- Firewall as a Service (FWaaS), which rolls up firewall technology into a cloud-based service
- Zero Trust Network Access (ZTNA), which applies zero trust security principles to remote traffic
- Cloud Access Security Broker (CASB), which applies enterprise security controls and policies to traffic between the cloud and on-premise networks
Several use cases are driving enterprises to adopt SSE, including securing traffic from remote workers. This allows the migration to cloud and SaaS platforms while applying the same level of security as on-premises, and simplifying the security of an SD-WAN architecture. Let’s dive into the top SSE use cases and benefits for enterprises.
Top SSE use cases and benefits for enterprises
The top use case driving SSE adoption, and the most relevant to many enterprises right now, is the need to provide secure and reliable access for remote employees. We’ll also touch upon how SSE enables secure adoption of cloud and SaaS solutions and how you can combine SSE with SD-WAN technology to achieve the SASE model.
SSE use case #1: Securing remote access for remote employees
The pandemic forced many enterprises to adopt new remote access technologies—or upgrade existing ones—so their employees could safely work from anywhere without affecting productivity. However, even pre-pandemic, many organizations were recognizing the limitations of VPNs (virtual private networks) for a workforce that might need access to enterprise resources from anywhere in the world at any time. VPNs present numerous security challenges for enterprises:
- To secure remote traffic, you need to route it through a firewall or security appliance at your headquarters or data center. This can create significant bottlenecks on your enterprise network and affect performance for both remote and on-premises users.
- Typical VPN solutions don’t provide any mechanism for centrally managing your deployments or monitoring the devices that remotely connect to your network. For an enterprise setting, it means you could be allowing hundreds or thousands of remote VPN connections to your primary enterprise network, from devices that may or may not have adequate security controls without verifying the identity or trustworthiness of the person connecting.
- In addition, once a user or device connects via VPN, they can freely move about your enterprise network just as if they were in the office. If a hacker compromises a privileged account with VPN access, they could jump from system to system, exfiltrating data and causing financial and reputational damage in the process.
SSE benefits for securing remote connections of enterprises, cloud, and SaaS services
Enterprises can significantly reduce bottlenecks by bypassing their headquarters since most remote traffic is destined for services outside the network. SSE eliminates the need for remote, cloud, or web-destined traffic to route through the enterprise network firewall, because it provides security as a cloud-based service. That means you’re routing remote traffic through an SSE solution in the cloud, rather than a physical device through the office or data center, reducing the enterprise network’s load.
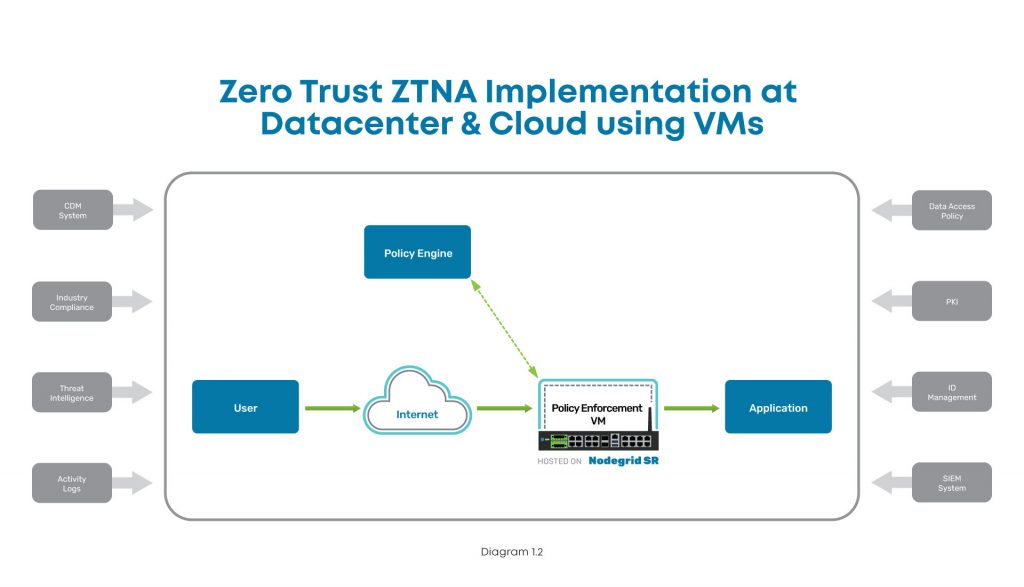
SSE uses technology like ZTNA to provide granular visibility, control, and verification of all the remote users and devices connecting to the enterprise resources. For example, with ZTNA, you can apply specific access control policies that grant remote users access to only the specific resource they need for the task at hand. Once a remote user authenticates, ZTNA creates a secure, encrypted tunnel to that application or resource, removing the need for a VPN.
SSE also provides a unified, cloud-based security stack that you can access and manage from anywhere at any time. Through components like FWaaS, you can monitor and track all remote devices from one control panel. For instance, you can ensure all laptops are running the latest security definitions and create rules that block connections from a device that isn’t up-to-date.
In addition, SSE restricts lateral movement on your network, following what’s known as the “dark cloud” principle (also known as software-defined perimeter) to prevent remote users from seeing or interacting with anything except the specific application they’ve been authenticated for. If a remote user needs to access a different resource, their privileges and trustworthiness can be re-verified using specific security policies for that new resource.
SSE addresses VPNs’ security concerns, by providing an alternative way for remote users to securely access the cloud, SaaS, and web services they need without contacting your enterprise network. Using technologies like ZTNA and FWaaS, SSE allows you to centrally manage the remote users and devices, apply highly precise security policies, and restrict lateral movement on the network, while still providing secure and reliable access to enterprise resources. That’s why you should consider replacing VPN with SSE for the work-from-anywhere user base.
SSE use case #2: Public cloud and SaaS adoption without sacrificing security
Security is one of the primary concerns when migrating workloads or services to the cloud. For example, you may find it challenging to apply enterprise security and access control policies to your SaaS or cloud platform, leading to inadequate policy enforcement in the name of convenience.
Another example is when you process regulated data for healthcare or financial systems; you may need to enforce specific data governance policies about who can access what information for which reasons. It can be challenging to gain visibility on how your users are accessing data in the cloud, mainly if you rely on the monitoring functionality provided by individual cloud vendors.
SSE benefits for securing public cloud and SaaS implementation
Cloud and SaaS services need the same level of security as your enterprise network, and SSE makes that possible. SSE uses an integrated CASB to apply enterprise security, access, governance, and compliance policies across all cloud and SaaS platforms. The CASB also uses an API integration to automatically discover data, both at rest and in transit, across all cloud services so you can easily see who is accessing it and how it’s being used. This API integration allows the CASB to scan for malware and policy violations, send alerts, and automatically remediate threats.
SSE doesn’t just benefit remote workforces. Using an integrated CASB, SSE also allows enterprises to migrate from on-premises data centers to cloud and SaaS platforms while applying the same security, access, and data governance policies. We recommend adopting SSE if you’re migrating any critical or sensitive resources to the cloud.
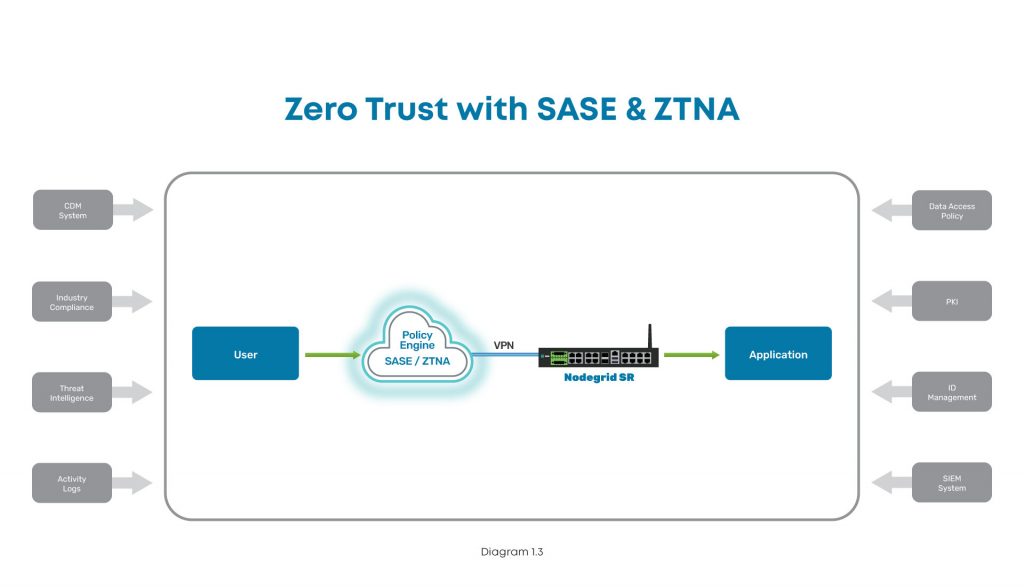
SSE use case #3: Combining SSE with SD-WAN to achieve SASE
Secure access service edge, is a popular network security model introduced by Gartner in 2019. SASE combines a cloud-based security stack with software-defined wide area network (SD-WAN) technology to provide an integrated solution for accessing and securing your network edge.
The SASE stack includes the same technologies as SSE, and you’ve probably noticed the names are very similar. That’s because SASE is essentially SSE plus access—which is provided by an SD-WAN backbone.
Benefits of combining SSE with SD-WAN to achieve the SASE model
There are numerous benefits to implementing both SD-WAN and SSE to achieve the SASE model. For one, SSE doesn’t provide any mechanism to connect your remote and branch office users to the cloud and SaaS resources it’s protecting. SD-WAN’s intelligent and application-aware routing lets you send remote traffic directly to your cloud and SaaS platforms and bypass your enterprise network.
In addition, SD-WAN technology doesn’t come with any mechanisms for security—you still need to use firewalls and other appliances at all your data centers and branch offices to protect that traffic. The more remote locations you add to your SD-WAN implementation, the more security appliances you need to manage. SSE simplifies things by consolidating all your SD-WAN security into a single cloud-based stack.
SSE and SD-WAN complement each other well, and when you combine them, you end up with a comprehensive SASE implementation. If you have an existing SD-WAN architecture and want to simplify and streamline your network security, then you should add SSE to achieve full SASE. And the reverse is also true—if you’re going to implement SSE but don’t have the existing architecture for enabling remote and branch office access, then you should consider SD-WAN technology.
Accelerate your SSE deployment with Nodegrid
If you’re looking for a better way to secure remote traffic, cloud resources, and SD-WAN architecture, then your enterprise may benefit from a security service edge. Suppose you don’t already have an SD-WAN backbone on which to build SSE implementation. In that case, consider a vendor-neutral platform that works with a security service edge provider. ZPE Systems’ Nodegrid partners with top SSE providers, including Palo Alto, to provide a seamless SD-WAN onramp to your security service edge functionality. The Nodegrid SD-WAN platform for enterprise networks is key to making SSE work for your enterprise.
Want to learn more about how Nodegrid can help support your SSE use case?
Contact us online or call 1-844-4ZPE-SYS today.



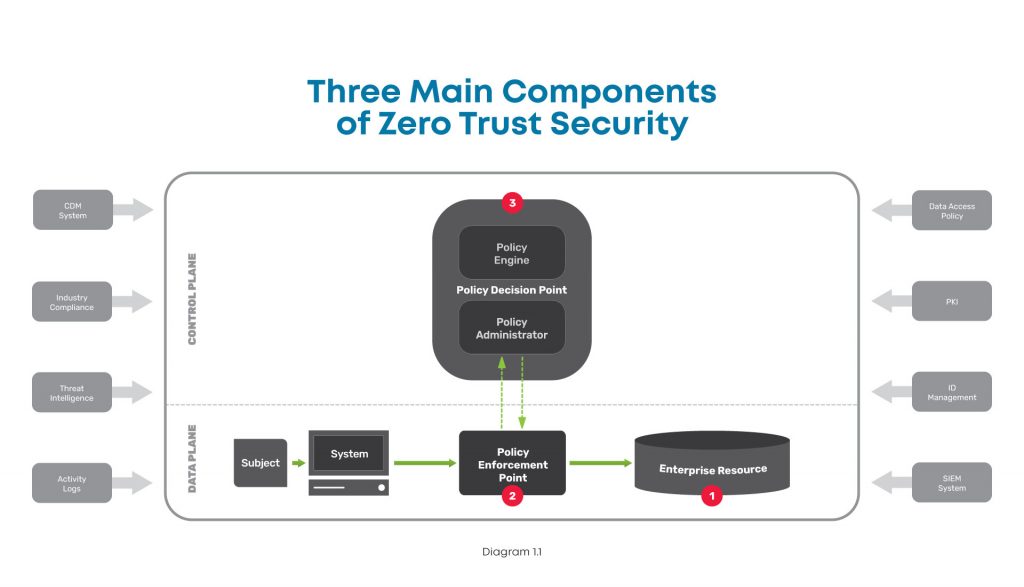


 One of the fundamental goals of networking is to allow the flow of information between computers, people, and organizations. However, that information is becoming more decentralized and must be relayed through various channels, which increases risk. Since traditional security architectures simply can’t provide omnipresent protection for data and communications, organizations around the globe are adopting zero trust security.
One of the fundamental goals of networking is to allow the flow of information between computers, people, and organizations. However, that information is becoming more decentralized and must be relayed through various channels, which increases risk. Since traditional security architectures simply can’t provide omnipresent protection for data and communications, organizations around the globe are adopting zero trust security.