Cloud-Delivered Branch: Simplifying Remote Management
The cloud-delivered branch is a relatively new concept that provides branch networking, security, and management solutions as a cloud-based service. The idea is to simplify remote management by reducing the number of individual solutions deployed at each branch and allowing admins to monitor and control all of their branches from a single place. This is like giving teams one single toolkit that can service every branch.
This post describes the three cloud-based services involved in a cloud-delivered branch, and gives an example of how to implement a cloud-delivered branch using the Nodegrid platform from ZPE Systems.
To see examples of a cloud-delivered branch in action, request a free demo of the Nodegrid platform.
How a cloud-delivered branch simplifies remote management
There are three key components of a cloud-delivered branch: cloud-based infrastructure management, cloud-based network management, and cloud-based cybersecurity. Let’s discuss the technologies used in each component.
Cloud-managed branch gateways
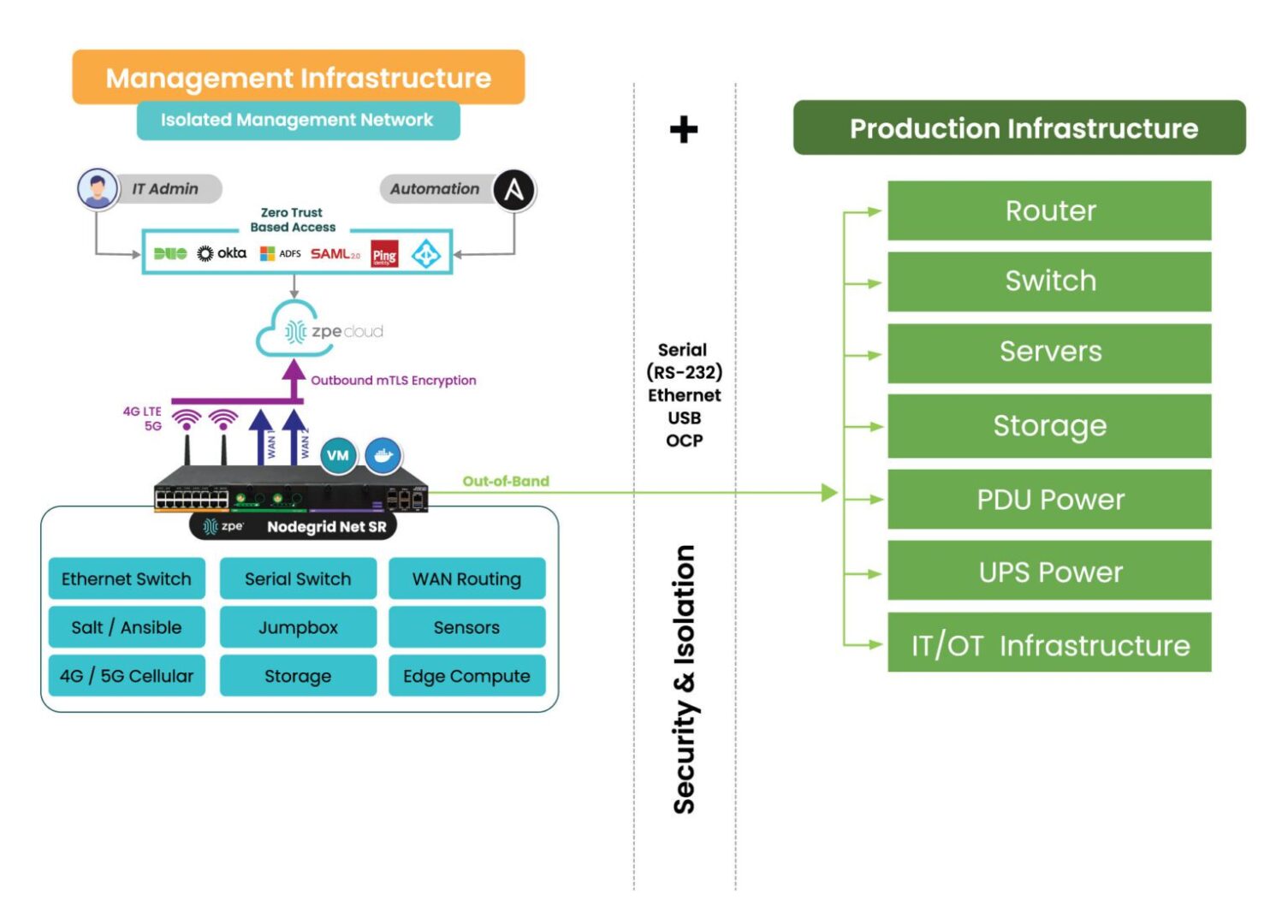
A branch gateway is a networking device that lives in the branch and provides access to the enterprise WAN as well as cloud resources and the internet. A gateway that’s optimized for branch networking will usually combine multiple network functionalities in one to save rack space and reduce complexity. For the purposes of the cloud-delivered branch, one of these features should be device management, i.e. serial console/console server technology. This functionality means that any infrastructure component connected to the gateway, whether it’s via RJ-45 or Wi-Fi, can be remotely managed by simply logging into the gateway’s software, reducing the need for a jump box or dedicated management hardware. Of course, what makes it a cloud-managed branch gateway is that admins manage it (and all connected infrastructure) from a cloud platform instead of directly connecting to the gateway over the WAN. This means that admins have management access from anywhere in the world, without needing to be on the enterprise network.
|
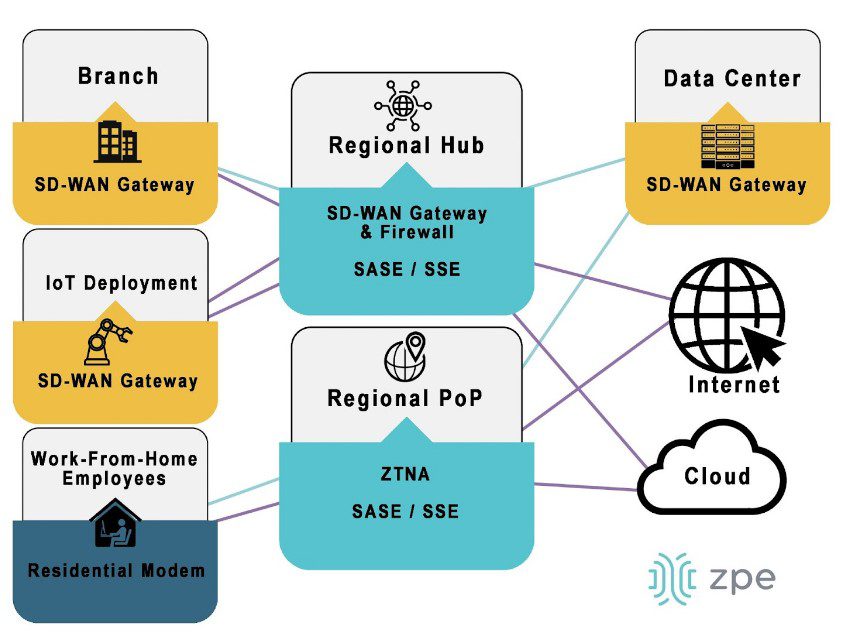
Software-defined wide area networking (SD-WAN)
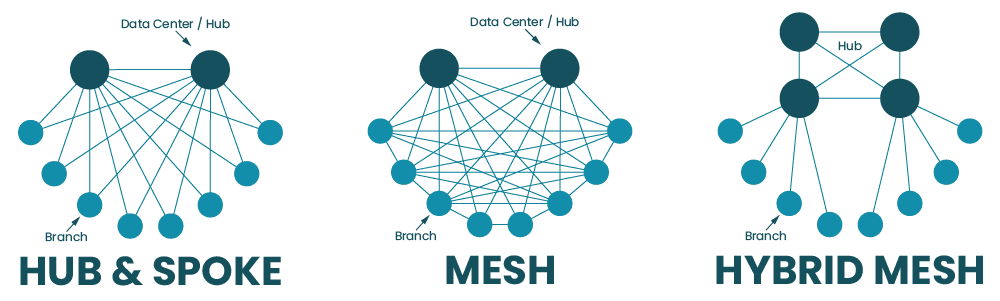
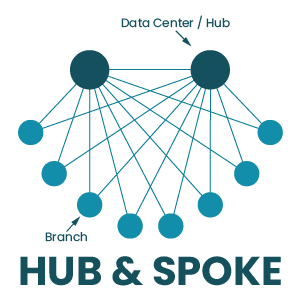
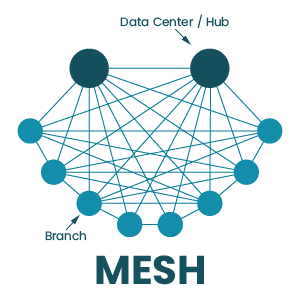
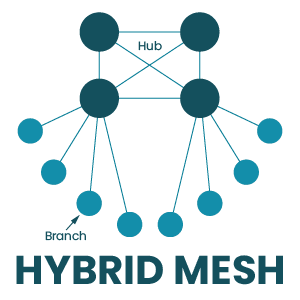
SD-WAN, or software-defined wide area networking, simplifies WAN management by decoupling control functions from the underlying hardware and making them available as software. Essentially, SD-WAN splits a WAN architecture into two layers: the physical hardware that connects branches to the enterprise network (e.g., cloud-managed branch gateways), and the networking logic that orchestrates WAN traffic (e.g., routing rules and load balancing). In a cloud-delivered branch, SD-WAN’s software lives in the cloud, giving network teams a centralized place from which to monitor and control the entire WAN architecture, no matter how many branches are involved.
|
Secure Access Service Edge (SASE)
SASE (pronounced “sassy”) is a solution that combines multiple enterprise security technologies into a single stack that’s delivered as a cloud-based service. SASE uses SD-WAN technology to directly connect branch users and devices to enterprise resources in the cloud, first passing that traffic through the SASE stack to ensure that security policies and controls are applied. That means this traffic doesn’t need to go through a traditional firewall, which reduces bottlenecks at the central data center without requiring a security appliance at each branch. Eliminating firewalls at most branches decreases management complexity for network admins, and reducing the load on a centralized data center firewall improves performance for the entire enterprise.
|
How to implement a cloud-delivered branch with Nodegrid
A cloud-delivered branch uses cloud-based infrastructure management, network management, and security to simplify remote branch management. The best practices for building infrastructure to support a cloud-delivered branch include:
| Best practices: | Benefits: |
| Using vendor-neutral hardware and software solutions | Reduces the number of infrastructure devices that need to be deployed
Enables unified, centralized infrastructure management Supports third-party apps and automation |
| Implementing out-of-band (OOB) management at each site | Provides an alternative path to critical remote infrastructure during WAN/LAN outages
Reduces the frequency and cost of truck-rolls Ensures that resource-intensive automation workflows don’t cause production latency |
| Incorporating branch LAN management into the cloud-management umbrella | Extends software-defined networking control into the branch LAN
Unifies branch WAN and LAN management behind a single pane of glass Increases efficiency and ensures holistic coverage |
Let’s walk through an example of how these best practices are implemented using the Nodegrid platform from ZPE Systems.
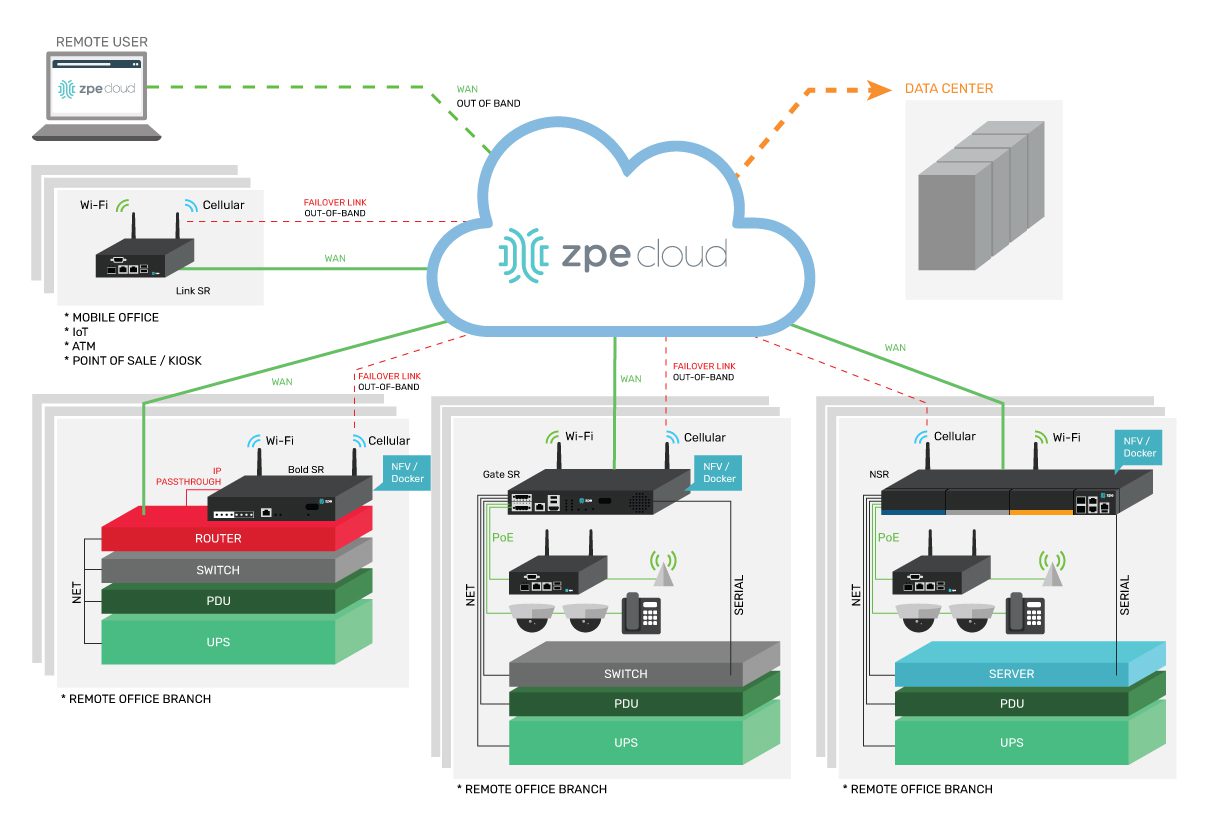
Vendor-neutral branch gateways and cloud management
A Nodegrid branch gateway such as the Bold Services Router is installed at each branch to provide WAN and internet access. These all-in-one networking solutions provide routing, switching, and console server management functionality, reducing the number of infrastructure devices that need to be deployed. All Nodegrid devices are completely vendor-neutral, which means you can use them to host your SD-WAN, SASE, or edge computing applications, saving you from buying and installing additional hardware. In addition, vendor-neutral Nodegrid gateways unify branch infrastructure management through the ZPE Cloud software. Any infrastructure connected to a Nodegrid device at any branch is available to manage through ZPE’s centralized, cloud-based platform, simplifying remote management and providing greater opportunities for optimization and automation. Plus, ZPE Cloud software is also vendor-neutral, meaning you can integrate third-party apps and tools to create a fully customizable infrastructure and network orchestration platform.
Gen 3 out-of-band management
One of the most challenging aspects of remote branch management is recovering from network outages without any technical staff on-site to reboot devices or refresh IP addresses. Out-of-band (OOB) management solves this problem by providing an alternative path to critical remote infrastructure that doesn’t rely on the production WAN or LAN. Teams use OOB management to troubleshoot and fix problems and recover from outages, reducing the need for costly truck-rolls. Nodegrid branch gateways provide Gen 3 OOB management capabilities, the most advanced form of OOB technology. Nodegrid gateways are considered Gen 3 because they support third-party infrastructure and network automation via the OOB network. That means teams can use their preferred scripting languages and tools to execute resource-intensive automation workflows on a management network that’s completely separate from the production network. For example, admins can run AIOps root-cause analysis tools to fix problems, or orchestrate automation device provisioning, without taking up valuable MPLS bandwidth or creating additional latency on the production LAN. Additionally, companies typically need a jump box at every branch to host all their troubleshooting, remediation, and automation tools. The benefit of vendor-neutral Nodegrid devices is that they become a one-stop shop for OOB as well as all the services and tools you’d normally install on a jump box. This eliminates the need for separate out-of-band management and jump box appliances.
Branch LAN management with SD-Branch
SD-WAN provides software abstraction and cloud management for WAN architectures, but it typically stops at the edge of the branch, meaning admins use a different solution to manage the internal branch LANs. Nodegrid gateways extend software-defined networking control into the branch LAN using technology called SD-Branch. That means teams can use the same ZPE Cloud platform to control every aspect of branch networking, creating a streamlined management environment that increases efficiency and ensures holistic coverage. Using a Nodegrid device for your cloud-delivered branch reduces the number of network solutions deployed at each site, standardizes branch network management, and increases your automation and orchestration capabilities. Deploying fewer boxes decreases the cost to spin up a new branch, while standardization and automation helps to reduce operating expenses and increase operational efficiency.
Ready to learn more about implementing a cloud-delivered branch?
To learn more about implementing a cloud-delivered branch with Nodegrid, contact ZPE Systems today.