Orchestrating Hybrid Network Environments: Challenges, Solutions, and Best Practices
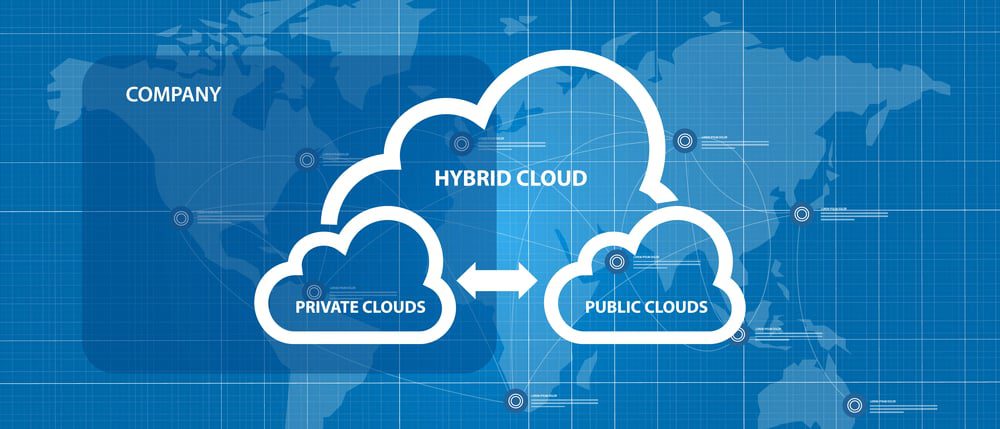
A hybrid network environment combines infrastructure from a public cloud with a private cloud and/or on-premises deployment. Your compute, storage, and service resources are distributed across multiple locations and platforms and connected via WAN (wide area network).
A hybrid network deployment aims to create a single, unified environment of workloads and resources that you can easily move around as needed for failover or performance optimization. However, accomplishing this goal in such a complex network architecture while avoiding vendor lock-in and maintaining consistent security is very challenging.
This blog discusses the challenge of orchestrating hybrid network environments as well as the solutions to help you overcome these difficulties.
The challenge of orchestrating hybrid network environments
To efficiently manage and utilize a hybrid network environment, you’ll need to overcome three major hurdles, including:
Vendor lock-in
A hybrid network environment generally includes devices, platforms, and services from multiple vendors in multiple locations. Often, these solutions are designed to work in closed ecosystems, meaning they don’t integrate well with other vendors’ platforms. This makes it challenging to connect cloud and on-premises resources and create a unified hybrid environment. It also creates difficulties with implementing third-party automation and centralized orchestration.
Complexity
Hybrid network environments are more complex than legacy networks because critical infrastructure is distributed both physically and logically. This requires comprehensive monitoring and reporting of devices, traffic, and user activity in locations to which you have minimal access. It also requires more sophisticated networking to ensure end-users have seamless access to applications and resources. Without automation and centralized orchestration, monitoring and controlling network routing, infrastructure, and security across a hybrid environment is challenging.
Security
To keep your entire hybrid network environment secure, you need to apply enterprise security policies consistently across your on-premises, data center, and cloud infrastructure. This consistency is difficult to achieve in the cloud because legacy security controls aren’t always compatible with cloud infrastructure. Often, that means you need to implement separate policies and solutions for your on-premises and cloud resources. However, without a way to centrally manage your hybrid security architecture, this increases the likelihood of mistakes and configuration drift between cloud and legacy policies. It also adds complexity to hybrid network orchestration and takes you further away from your goal of creating a unified environment.
Often, organizations try to implement a separate set of security policies and controls for their cloud infrastructure. However, this increases the likelihood of mistakes and configuration drift between cloud and legacy policies. It also adds complexity to hybrid network orchestration and takes you further away from your goal of creating a unified environment.
Each of these challenges stems from a hybrid network environment consisting of multiple solutions from multiple vendors in multiple locations. The solution, then, is to reduce complexity by implementing a single, centralized orchestration platform that gives you visibility and control over your entire hybrid environment.
How to orchestrate hybrid network environments with a single platform
To ensure that your hybrid network orchestration platform will address these key challenges, you should look for the following characteristics:
Vendor neutral or vendor agnostic
Your hybrid network orchestration platform needs to be able to dig its hooks into every device, application, and vendor solution in your environment. That means it needs to be vendor neutral or vendor agnostic. This will give you centralized visibility into and control over your entire hybrid network. Vendor neutral orchestration also facilitates third-party automation, which helps reduce the risk of human error and creates a more streamlined NetDevOps environment.
Centralized, cloud-based control
This vendor neutral orchestration platform should roll up all your critical network management, monitoring, and automation functionality so your engineers can oversee your entire environment from behind one pane of glass. This centralized control panel should live in the cloud, so you can access your monitoring and orchestration from anywhere in the world without a VPN. A cloud-based orchestration platform ensures your engineers have access to view and troubleshoot your network even if an ISP or hosting provider suffers from an outage.
Integrated security
Securing your hybrid network might require upgrading pieces of your existing security architecture—such as identity and access management (IAM)—with solutions extending across both on-premises and cloud infrastructures. Other aspects of security (like firewalling) will likely require different solutions for on-premises and cloud, primarily because of the limitations of legacy systems when it comes to protecting cloud resources.
In addition, using cloud-based security solutions—such as Security Service Edge (SSE)—allows you to intelligently route remote, cloud-destined traffic from your branch and edge locations. This removes the need to backhaul traffic through your on-premises firewall, reducing network bottlenecks and optimizing performance.
Of course, to efficiently manage so many security solutions, you need centralized orchestration with vendor neutral security integrations with your IAM, SSE, on-premises firewall, and other security controls. This allows you to apply consistent security policies across your hybrid environment, which is critical for security best practices like zero trust. It also ensures that you can see a complete overview of your hybrid network security from one place, reducing the risk of an issue or alert falling between the cracks.
Using a single, vendor-neutral orchestration platform simplifies hybrid network management by providing a unified control panel to oversee your entire environment. A vendor neutral solution also enables third-party integrations with automation and security solutions to further reduce the complexity of hybrid network orchestration. The right hybrid network orchestration platform will allow you to create a unified environment that’s fast, reliable, and secure.
For example, the Nodegrid network management solution from ZPE Systems delivers orchestration control over hybrid network environments with complete vendor freedom. Nodegrid hardware runs on the open, Linux-based Nodegrid OS, allowing it to “say yes” to every vendor solution and platform in your hybrid architecture. ZPE Cloud provides a centralized, cloud-based platform so you can monitor and orchestrate your hybrid infrastructure from anywhere in the world.
The Nodegrid platform supports integrations with third-party automation solutions like Chef, Ansible, and RESTful so you can reduce manual interventions and increase efficiency. Plus, Nodegrid works seamlessly with leading IAM, zero trust, SSE, and other security providers, giving you a single pane of glass from which to orchestrate every piece of your hybrid network environment.
Learn more about orchestrating hybrid network environments
★ Benefits of SD-WAN for Hybrid Cloud Infrastructure
★ Why Choose Nodegrid as Your Data Center Orchestration Tool
★ Simplifying Network Edge Orchestration With a Single Platform
Orchestrating hybrid network environments is easier with Nodegrid.
Contact ZPE Systems to view a free demo.