What is zero trust security? This post defines the term and discusses its history before providing a guide to implementing zero trust in your organization.
Micro-segmentation
What is a radio access network (RAN)?
This post provides an introduction to radio access networks (RAN) before discussing 5G RAN challenges, solutions, and use cases.
Operational Technology Security
This guide defines OT, explains how to overcome some of the biggest operational technology security challenges, and discusses the importance of recovery in building resilience in OT.
Medical Devices Cybersecurity Risk
Discussing the factors that make medical devices a cybersecurity risk before providing mitigation strategies to help healthcare organizations.
Zero Trust Security Architecture
This post defines a zero trust security architecture, discusses some of the gaps typically left in such an architecture, and provides tips for avoiding these pitfalls.
The Biggest Ransomware Attack You Haven’t Heard of…Yet
The most successful ransomware attack ever is happening right now. See why isolated management infrastructure is the only way to save your organization.
How to Implement Zero Trust for OT
Zero trust for OT uses network segmentation, strong security policies, and advanced security technologies to protect operational technology from attack.
IoT in Finance Industry and Security Challenges
This post discusses how to take advantage of IoT in the finance industry by overcoming security challenges with automation, secure platforms, and vendor-neutral orchestration.
Best Intel NUC Alternatives
Discussing the challenges and security risks associated with Intel NUC jump boxes before providing enterprise-grade Intel NUC alternatives that solve these problems.
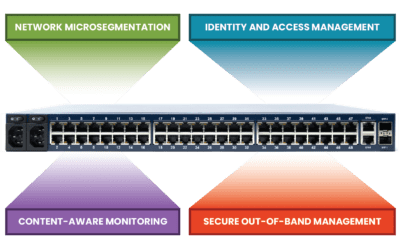
What Is a Zero Trust Gateway?
This post discusses the technologies that make up a zero trust gateway and explains how they work together to defend enterprise networks.