Opengear Lighthouse Appliances: Alternative Options
Lighthouse appliances are Opengear’s out-of-band management (OOBM) solutions for data center and branch deployments. Lighthouse refers to the on-premises software application used to monitor and control Opengear-connected infrastructure devices.
Opengear Lighthouse appliances are good second-generation solutions, but they suffer from a few major limitations that prevent organizations from fully automating and securing the control plane. This guide explains why you might consider Lighthouse alternatives before providing third-generation OOBM options from ZPE Systems that improve upon the four most popular Opengear models.
Why consider Lighthouse alternatives?
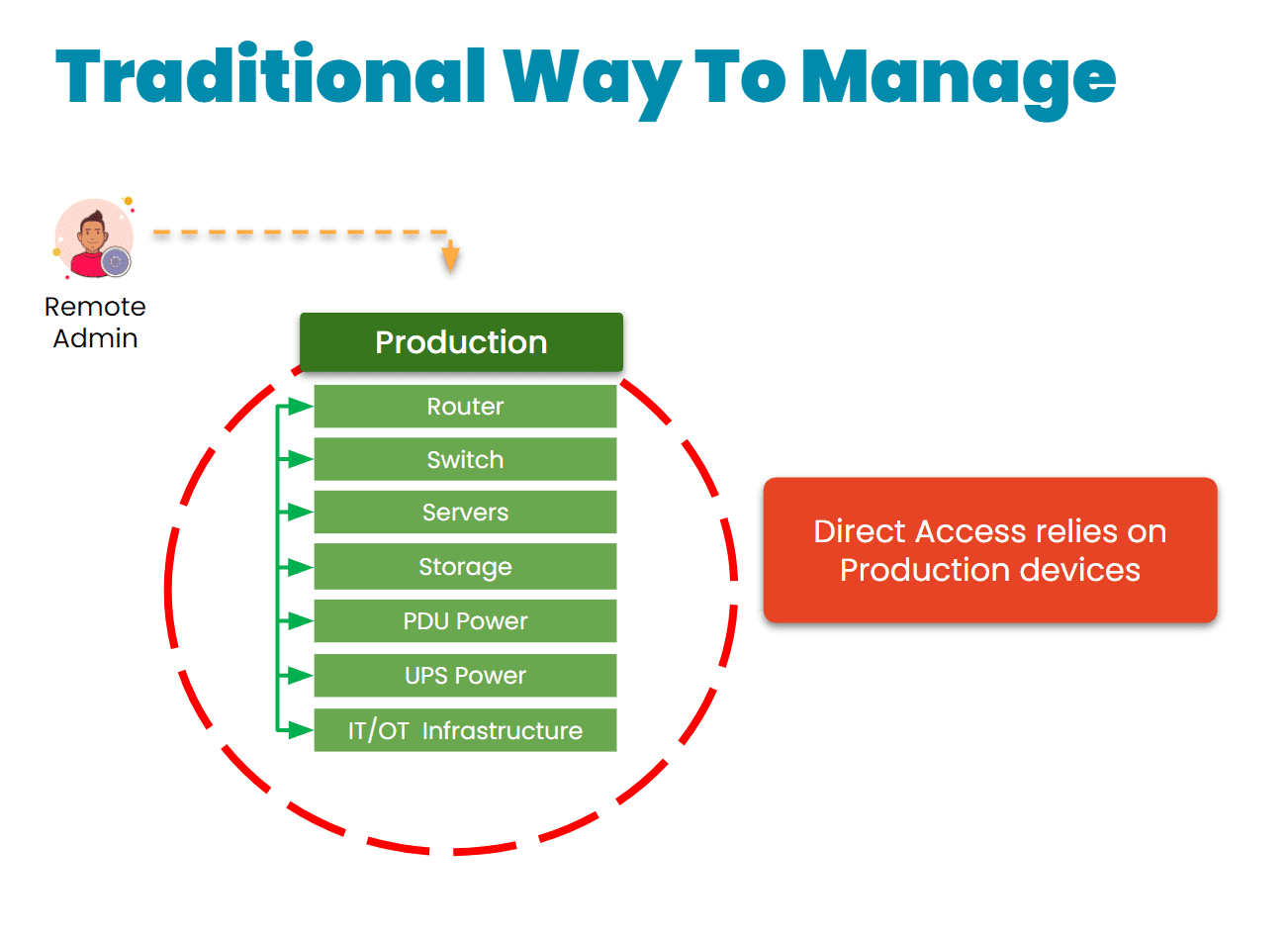
Lighthouse appliances are second-generation (or Gen 2) out-of-band management solutions that suffer from three major limitations:
- Much of their automation capabilities, such as Docker container hosting and Python scripts, are locked behind an upgraded version of Lighthouse.
- They do not support two-factor authentication (2FA) or SAML 2.0 authentication.
- Lighthouse appliances are not truly vendor-neutral, only supporting certain integrations and requiring software license upgrades for some capabilities.
These factors prevent teams from fully automating and securing their control plane. A lack of automation, security, and the ability to host third-party tools on the OOB network also limits an organization’s network resilience.
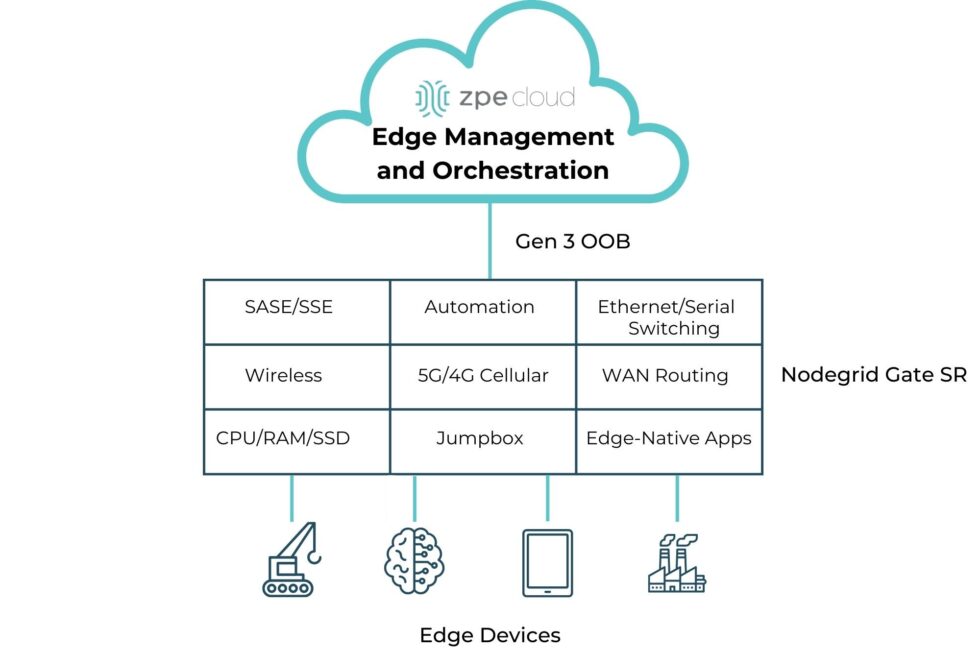
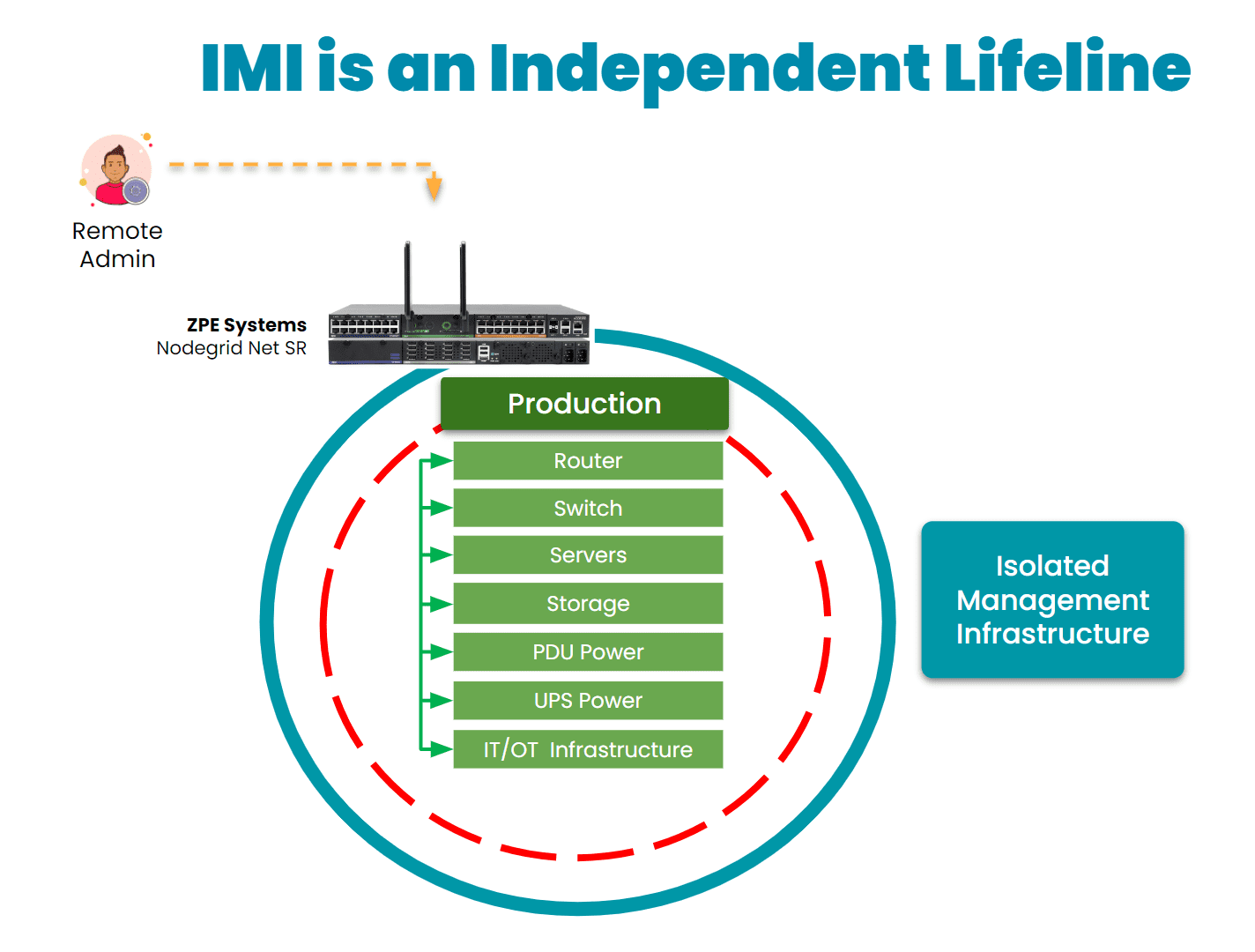
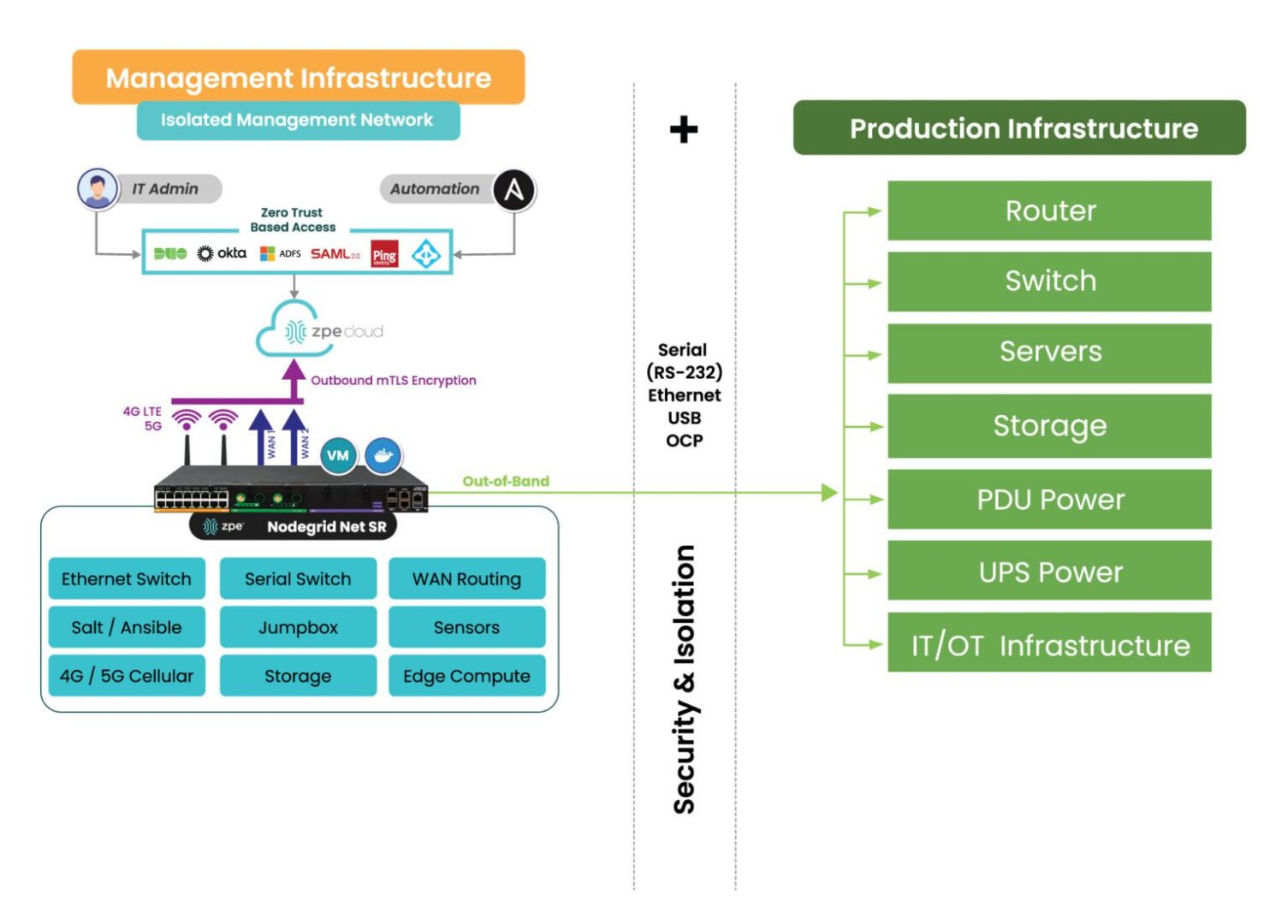
The Nodegrid platform from ZPE Systems fills these gaps with an open, Gen 3 architecture that enables end-to-end automation using powerful, all-in-one devices protected with robust on-board security features.
Nodegrid alternatives for Lighthouse appliances
ZPE Systems offers a wide range of Nodegrid appliances to meet almost any business need or use case. This guide highlights four Nodegrid models that serve as direct replacements for – or alternatives to – Opengear Lighthouse appliances.
Opengear CM8100 alternative: Nodegrid Serial Console Plus
The CM8100 is Opengear’s high-density appliance for large data center deployments. The Nodegrid Serial Console Plus (NSCP) improves upon the CM8100 in several key ways:
- The NSCP provides up to 96 managed serial ports in a 1U appliance, unlike the CM8100’s 96-port model which takes up two units of rack space.
- Its Intel x86 CPU and 4GB of RAM provide enough processing power to easily run 3rd-party Docker and VM apps while supporting 1,000+ concurrent serial sessions, beating out the CM8100’s ARM CPU and 2GB of RAM.
- It supports automation out of the box and extends zero-touch provisioning and other automation to legacy and mixed-vendor infrastructure, unlike Lighthouse which requires an enhanced license for most automation.
- Several NSCP models have dual-SIM cellular slots for failover and OOBM, but none of the CM8100 models support cellular.
- It supports a wide range of USB environmental monitoring sensors to help control conditions in remote data centers.
- Unlike the CM8100, it comes with robust security features like BIOS protection and GPS geofencing and also supports SAML 2.0 authentication.
Comparison Table: CM8100 Lighthouse Appliance vs. Nodegrid Serial Console Plus
| Nodegrid NSCP | Opengear CM8100 | |
|---|---|---|
| Serial Ports | 16 / 32 / 48 / 96x RS-232 | 16 / 32 / 48 / 96x RS-232 |
| Network Interfaces | 2x SFP+
2x ETH 1x Wi-Fi (optional) 2x Dual SIM LTE (optional) |
2x ETH |
| Additional Interfaces | 1x RS-232 console
2x USB 3.0 Type A 1x HDMI Output |
1x RS-232 console
2x USB 3.0 |
| CPU | Intel x86_64 Quad-Core | ARM Cortex-A9 1.6 GHz Dual-Core |
| Storage | 32GB SSD (upgrades available) | 32GB eMMC |
| RAM | 4GB DDR4 (upgrades available) | 2GB DDR4 |
| Environmental Monitoring | Any USB sensors | – |
| Form Factor | 1U Rack Mounted | 1U Rack Mounted (up to 48 ports)
2U Rack Mounted (96 ports) |
Opengear OM2200 alternative: Nodegrid Serial Console S Series
The OM2200 console server has software-selectable serial ports that allow administrators to manage devices with straight or rolled RS-232 pinouts for mixed legacy and modern infrastructures. The Nodegrid Serial Console S Series serves as a direct alternative that offers a few key advantages:
- The S Series has auto-sensing ports, further streamlining the management of mixed architectures.
- It comes with 14 high-speed managed USB ports, compared to the OM2200’s 8 USB ports.
- As with the NSCP, it supports automation out of the box, has cellular options (via USB connections to cellular modems), can use USB environmental sensors, and provides comprehensive security for the control plane.
Comparison Table: OM2200 Lighthouse Appliance vs. Nodegrid Serial Console S Series
|
Nodegrid S Series |
Opengear OM2200 |
|
|---|---|---|
|
Serial Ports |
16 / 32 / 48x Software Selectable RS-232 14x USB-A serial |
16 / 32 / 48x Software Selectable RS-232 8x USB 2.0 serial (OM2224-24E) 24x Software Selectable RS-232 and 24x Managed Ethernet |
|
Network Interfaces |
2x1Gbps or 2x ETH |
2x SFP+ or 2x ETH 1x V.92 modem (select models) |
|
Additional Interfaces |
1x RS-232 console 1x USB 3.0 Type A 1x HDMI Output |
1x RS-232 console 1x Micro USB 2x USB 3.0 |
|
CPU |
Intel x86_64 Dual-Core |
AMD GX-412TC 1.4 GHz Quad-Core |
|
Storage |
32GB SSD (upgrades available) |
64GB SSD |
|
RAM |
4GB DDR4 (upgrades available) |
8GB DDR3 |
|
Environmental Monitoring |
Any USB sensors |
– |
|
Form Factor |
1U Rack Mounted |
1U Rack Mounted |
Opengear CM7100 alternative: Nodegrid Serial Console Core Edition
The CM7100 is the previous generation of the CM8100 appliance, and it comes with several price-saving options (like smaller storage and RAM configurations) that make it popular for simple break-fix OOBM access to remotely troubleshoot and recover from issues.
ZPE Systems offers the NSCP Core Edition, a more stripped-down version of the Nodegrid Serial Console Plus. It improves upon the CM7100 in a few important ways:
- The NSCP-CE comes with analog modem and dual-SIM cellular options for network failover and OOBM, unlike the CM7100.
- Like the other Nodegrid models, it supports a wide range of environmental sensors, while the CM7100 supports specific sensors for smoke, water leaks, and vibration.
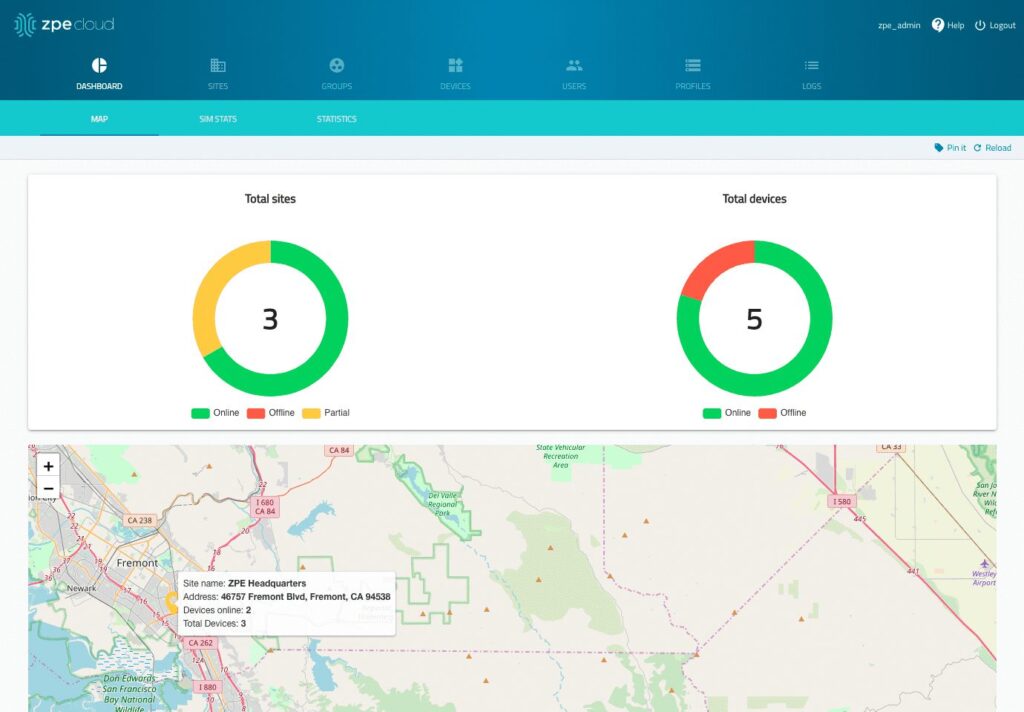
- As with the other Nodegrid models, it supports automation via ZPE Cloud, has cellular options, and provides comprehensive security for the control plane.
Comparison Table: CM7100 Lighthouse Appliance vs. Nodegrid Serial Console Core Edition
| Nodegrid NSCP-CE | Opengear CM7100 | |
|---|---|---|
| Serial Ports | 16 / 32 / 48 / RS-232 | 16 / 32 / 48 / 96x RS-232 |
| Network Interfaces | 2x SFP ETH 1x Analog modem (optional)
2x 5G/4G LTE (optional) |
2x ETH |
| Additional Interfaces | 1x RS-232 console
2x USB 3.0 Type A |
1x RS-232 console
2x USB 2.0 |
| CPU | Intel x86_64 Dual-Core | Armada 370 ARMv7 800 MHz |
| Storage | 16GB Flash (upgrades available) | 4-64GB storage |
| RAM | 4GB DDR4 (upgrades available) | 256MB-2GB DDR3 |
| Environmental Monitoring | Any USB sensors | Smoke, water leak, vibration |
| Form Factor | 1U Rack Mounted | 1U Rack Mounted (up to 48 ports)
2U Rack Mounted (96 ports) |
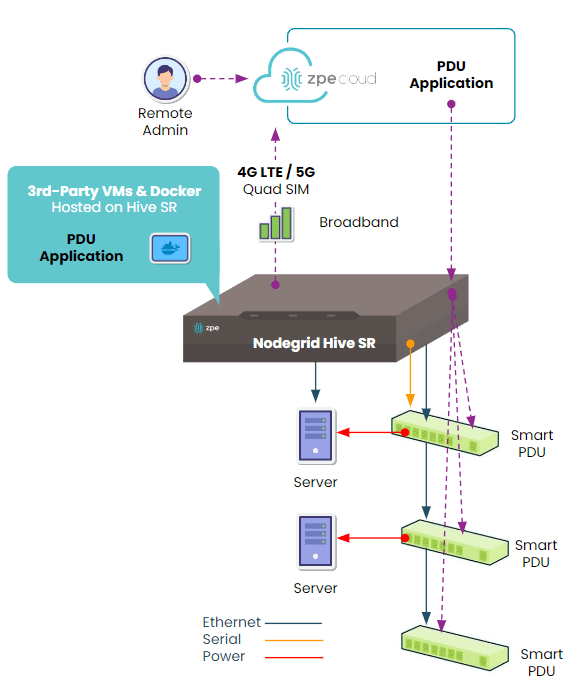
Opengear ACM7000 alternative: Nodegrid Gate Services Router
The ACM7000 Resilience Gateway provides gateway routing and OOBM for smaller deployments in branch and edge locations. The Nodegrid platform includes six multi-functional branch services routers available in various form factors and configurations to meet the needs of any organization. The Gate SR in particular makes an excellent replacement for the ACM7000 because it offers:
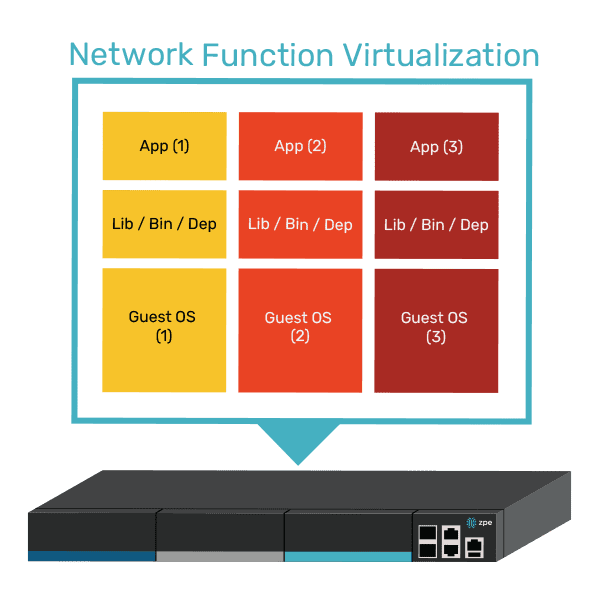
- Up to 4TB of storage to run up to 3 Guest OSes or 4 Docker applications.
- Optional dual-SIM 5G/4G cellular, while the ACM7000 only supports 4G LTE.
- The option for an embedded Nvidia Jetson Nano processor capable of running AI workloads, like those for computer vision, alongside traditional applications.
- Support for a wide range of environmental sensors, while the ACM7000 supports specific sensors for external water, smoke, and dry contact.
- Support for automation out of the box as well as comprehensive control plane security.
Comparison Table: ACM7000 Lighthouse Appliance vs. Nodegrid Gate Services Router
|
Nodegrid Gate SR |
Opengear ACM7000 |
|
|---|---|---|
|
Serial Ports |
8x RS-232 |
4 / 8x RS-232 |
|
Network Interfaces |
2x SFP ETH 1x Wi-Fi (optional) 2x Dual SIM LTE (optional) |
2 / 4x ETH 1x Single SIM LTE |
|
Additional Interfaces |
1x RS-232 console 4x ETH Switch 4x PoE ETH Switch 2x USB 3.0 Type A 2x USB 2.0 Type A |
1x RS-232 console 4x USB 2.0 |
|
CPU |
Intel x86_64 Dual-Core |
Armada 370 ARMv7 800 MHz |
|
Storage |
16GB Flash (upgrades available) |
4GB storage |
|
RAM |
4GB DDR4 (upgrades available) |
256MB DDR3 |
|
Environmental Monitoring |
Any USB sensors |
Smoke, water leak, vibration |
|
Form Factor |
1U Rack Mounted |
1U Rack Mounted |
Ready to upgrade to a Gen 3 OOBM appliance?
The Nodegrid platform from ZPE Systems offers third-generation automation, control, and security for the ultimate network resilience, improving upon Opengear’s outdated architecture. But we know that replacing Lighthouse appliances and other console servers takes a lot of effort. That’s why ZPE now offers a complete package of budget-friendly products and engineering services to help. Click here to see how we simplify the upgrade process.