Implementing a Network Modernization Strategy for Large-Scale Organizations

The importance of network modernization
Network infrastructure updates are expensive and can be disruptive, leaving many large companies wondering if the payoff is worth the risks. However, when COVID-19 struck, these organizations were left scrambling to replace their outdated and insecure VPN solutions with more robust remote connectivity technology. Similarly, in the current recession, enterprises that put off network modernization in the past are now finding themselves without the remote management and orchestration capabilities they need to keep their infrastructure running optimally with reduced staff. Even without the looming threat of major world disruptions, outdated network infrastructure poses a risk to large-scale organizations. Obsolete devices are no longer patched by the vendor, which means any vulnerabilities that exist will remain open for hackers to exploit. Older equipment is also more likely to break, and may not be supported by the provider, making it more difficult and expensive to recover from a failure. Plus, outdated infrastructure hampers an enterprise’s ability to innovate with new technologies to stay competitive in the market. Upgrading network infrastructure is expensive, time-consuming, and requires careful planning to prevent business interruption. However, investing in network modernization now will save you from more costly disruptions in the future.
A network modernization strategy for large-scale organizations
Enterprises need to carefully plan their path to network modernization to ensure they can meet their customer SLAs by avoiding outages and performance degradation. Here are some tips for implementing a network modernization strategy that minimizes disruption while leaving room for future growth.
Bridge the gap with a vendor-agnostic platform
To ensure a smooth upgrade process, organizations will gradually upgrade their infrastructure by replacing individual solutions one at a time. There’s typically an extended window of time in which there are both legacy and modern devices that need to be monitored, managed, and supported. This creates additional complexity for administrators who need to learn how to use the new solutions, integrate them with the existing infrastructure, and ensure there’s little-to-no impact on end users. It’s especially challenging when they need to use different management platforms to access and control each solution. That’s why it’s important to implement a vendor-agnostic network management platform that supports legacy and multi-vendor solutions. A vendor-agnostic platform gives administrators a single pane of glass from which to control the entire heterogeneous network architecture, simplifying day-to-day management and allowing them to focus on optimizing performance and implementing future upgrades. Plus, a unified platform makes it possible to extend new technological capabilities (like remote OOB management and automation) to older infrastructure, accelerating network modernization efforts.
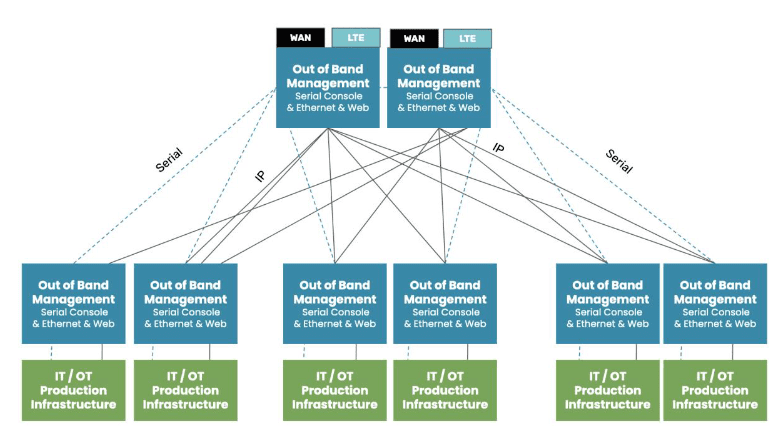
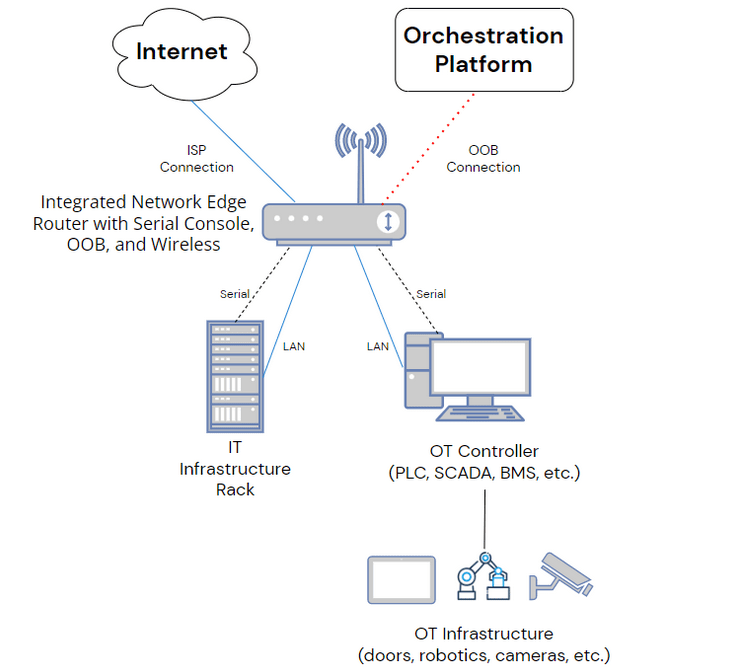
Reduce downtime with remote out-of-band management
Any experienced admin knows that installations and updates are risky procedures. Even with the best-laid plan, errors can occur that prevent new systems from coming online, cause integration issues with existing infrastructure, or even take down dependent network services. The risk is even greater when the upgrades occur remotely without any technicians on-site to power cycle devices or reconfigure systems offline. What if there’s an outage or severe disruption, but COVID lockdowns or natural disasters prevent staff from entering these locations? Remote out-of-band (OOB) management creates an alternative path that admins use to access remote infrastructure. It creates an out-of-band network that’s dedicated to infrastructure management and orchestration and that doesn’t rely on the availability of the production network. That means administrators can access and troubleshoot offline devices remotely, reducing the duration and impact of downtime. Remote OOB management makes it safer for large-scale organizations to implement a network modernization strategy and ensures the continued stability and availability of enterprise infrastructure.
Streamline deployments with automation
Even when new infrastructure deployments run smoothly, they take considerable time and effort on the part of network administrators. Large, global organizations have complex and highly distributed network architectures with thousands of moving parts that need to be upgraded or replaced. Just configuring and installing all of these new solutions can add significant delays to the network modernization process. Plus, configuring so many devices is tedious and prone to human error, causing more delays as admins troubleshoot and fix deployment failures. For example, a typo in an IP address on one device could prevent dependent services from deploying correctly, forcing teams to retrace their steps and waste time identifying the error. Automation is the key to streamlining device deployments and reducing configuration errors. For example, Zero Touch Provisioning (ZTP) allows admins to provision new devices automatically over the network using definition files. These files can be reused as many times as needed to deploy many identical solutions across the enterprise network, significantly reducing the time and effort required to modernize infrastructure. Plus, configuration files can be tested pre-deployment to ensure there are no errors or security vulnerabilities. Vendor-agnostic network management platforms, OOB management, and automation are crucial components of a smooth network modernization strategy. Implementing this strategy is easier if you choose a management solution that integrates all these capabilities into a single, unified platform.
Make Nodegrid a part of your network modernization strategy
The Nodegrid platform from ZPE Systems delivers vendor-agnostic control, Gen 3 OOB management, and end-to-end network automation capabilities in a single box. Nodegrid has helped large-scale organizations like the Internet Association of Australia update their network infrastructure without disrupting business. Nodegrid serial consoles support both legacy and modern Cisco pinouts, allowing them to dig their hooks into any device in your network infrastructure. That means you can use the ZPE Cloud solution to extend automation and orchestration to your entire heterogeneous architecture, supercharging your network modernization efforts. Nodegrid uses high-speed OOB interfaces (e.g., 5G/4G cellular) to provide admins with a fast and reliable connection for remote upgrades, management, and orchestration. Nodegrid allows you to power cycle devices, enter BIOS menus, manage power load distribution, and more from anywhere in the world with an internet connection. This makes it easier and safer for large-scale organizations to remotely upgrade their network infrastructure and ensures continuous management availability to prevent downtime in the future. The vendor-agnostic Nodegrid platform also allows you to extend automation features like ZTP to both legacy and modern solutions in your network infrastructure. Nodegrid supports integrations with your choice of third-party automation tools, or you can use Nodegrid hardware to directly host custom scripts and automation apps. This both streamlines the network modernization process and gives you the ability to grow and evolve your network with emerging automation technologies like AIOps. Nodegrid streamlines network modernization strategies by providing vendor-agnostic management, remote OOB management, and end-to-end automation support in a single platform.
Want to learn more about Nodegrid’s role in enterprise?
To learn more about Nodegrid’s role in an enterprise network modernization strategy, contact ZPE Systems today. Contact Us