CIOs: 3 Boardroom Questions to Survive Winter Recession & Lockdowns

We all know that company revenue is directly tied to IT infrastructure and the digital services it provides. In the simplest terms: network down, revenue down. So when economic downturns lead to hiring freezes and increasing workloads for IT, CIOs need to figure out how to ‘do more with less’ in order to maintain service levels. The reality is that we’d still expect IT to fulfill our support tickets even during the zombie apocalypse.
Today, business leaders are gearing up for the possibility of such challenges looming larger on the horizon, not to mention the potential for more covid lockdowns and other disruptions. No matter the reason, the expectation remains the same – keep networks reliable and secure.
Business leaders are uncertain about the coming winter
Business leaders are growing uncertain about the coming winter months because of the potential for more major operational shakeups, like those that occurred at the start of the coronavirus pandemic in 2020. This uncertainty stems from two looming possibilities:
- A winter recession, which economists predict is more likely as inflation increases. This will force business leaders to freeze hiring and keep operations running with limited staff on hand.
- A covid resurgence, which experts predict could lead to up to one million daily cases in the United States alone and infect 100 million Americans. Having more than one-third of the adult population unable to work for weeks at a time will leave infrastructure minimally maintained, leading to service downtime and revenue loss.
As CIO, your peers will ask how you plan to increase top line revenue despite the winter recession, limited staff numbers, and potential lockdowns. This means you’ll need solid answers to three critical questions that will come up at your next board meeting.
3 Questions to Help CIOs Survive the Winter Recession
If we need to freeze hiring, can we continue to fulfill SLAs for internal & external digital services?
The IT workload has grown exponentially since infrastructure moved from centralized to decentralized. There’s just too much infrastructure scattered in so many data centers, colocations, and branch offices — from servers and routers, to branch gateways, remote sensors, smart building infrastructure, user experience monitoring applications, and firewalls. On top of this, pushing workloads to edge compute and 5G will inevitably lead to more micro and nano data centers that need to be maintained. Your IT teams are already struggling to keep up with everyday operations like configuration management, troubleshooting, and recovering down equipment. Now imagine how much stress they’ll endure if they’re unable to get additional help due to hiring freezes or pandemic lockdowns.
If staff can no longer physically access equipment, can we maintain IT availability?
As we saw at the beginning of the Covid pandemic, companies scrambled to find ways to accommodate normal operations while shifting staff to a fully digital workplace. But many companies were unprepared and are still struggling to adapt. In fact in 2021, IT organizations reported that their highest priority was to improve digital work for employees, but 66% said they didn’t have the capabilities to support the needs of remote and hybrid work. IT organizations must be prepared to accommodate flexible work well into the future, but this typically means employing a mix of local smart hands, third party service providers, and remote management solutions that significantly inflate operating costs. Despite any potential lockdowns, physical access can already be challenging when equipment resides at remote locations that are costly, inconvenient, or downright dangerous to access.
Will we be able to stay in compliance and keep up with security patches?
Many security breaches occur not because patches don’t exist, but because installing these patches might lead to unforeseen breakages. Some IT teams still run software that’s years old and several major revisions outdated. Meanwhile, these teams can only hope that vulnerabilities won’t be exploited and lead to business incurring regulatory fines or penalties. In a nutshell, systems go unpatched and grow more vulnerable as time goes on, because teams are afraid to risk breakages that they can’t easily recover from. This problem will only worsen when hiring is put on hold and physical site access is restricted.
Big tech has it figured out
Big tech companies have thrived on recessions and often come out stronger. How? Because they understand that they must empower their IT organizations during economic downturn. According to Gartner, there’s no better way to do this than to invest in digital transformation. But exactly what digital investments do these companies make? As CIO, you have such a large and distributed IT organization to wrap your arms around, that it’s difficult to define the practical steps you need to take. When answering these three key questions, your IT and executive teams will need to know: “How do you plan to accomplish this?”
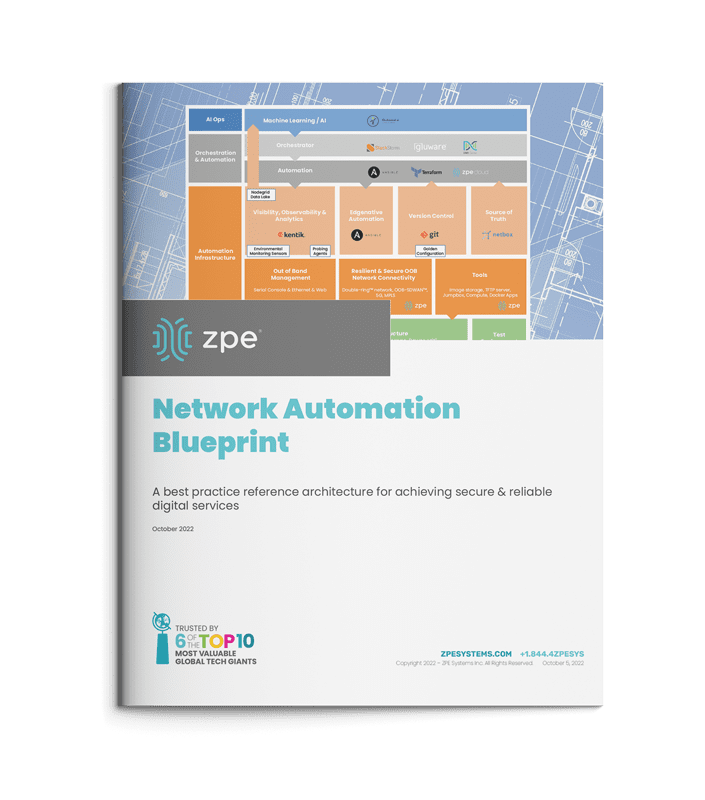
Use big tech’s secret: The Network Automation Blueprint
The network automation blueprint is made up of four major building blocks that create a management network design pattern to accommodate hyperautomation. These building blocks are:
- IT/OT production infrastructure: This includes servers, switches, routers, and common production equipment.
- Automation infrastructure: This is a truly independent network that enables automation to reach the production infrastructure in an out-of-band fashion. Customers call this the double-ring network. This layer often uses a combination of serial console and Ethernet connections, and also includes staging jump boxes, local storage, TFTP source of truth, and version control systems.
- Orchestration and automation systems: This is where the desired outcome and playbooks are sourced from. The key is that the orchestration reaches the production systems through the independent out-of-band network to achieve the desired outcome.
- AI Ops infrastructure: This layer receives rich information from observability platforms to make reactive and predictive decisions at scale. Using machine learning and artificial intelligence, this layer learns the network’s normal behaviors and pushes changes through the orchestration and automation layer.
This blueprint is the reference architecture validated to successfully implement Gartner’s definition of hyperautomation, as well as meet the Open Networking User Group (ONUG) Orchestration and Automation recommendations. This blueprint gives you the necessary layers to confidently answer the three questions that will come up during your boardroom meeting, and outlines the practical steps required to achieve IT resilience. Here’s how it answers these questions:
If we need to freeze hiring, can we continue providing reliable IT services?
By separating the automation infrastructure from the production network, teams can build hyperautomated environments while having a safe way to recover from errors. Despite having limited staff and/or a virtual workforce, teams can develop their automation pipelines to reduce workloads and meet SLAs.
If staff can no longer physically access equipment, can we maintain IT availability?
With the network automation blueprint, teams get a management network design pattern that ties into all of their solutions. This means they get a full virtual presence to manage SD-WAN, firewalls, switches, servers, routers, and their entire stack. The blueprint also calls for running automation locally so workloads can be carried out despite connectivity problems. These allow teams to maintain their sites and availability across distributed architectures.
Will we be able to stay in compliance and keep up with security patches?
Automating via out-of-band means teams no longer need anxiety about the dreaded Friday night upgrade. Instead of running outdated software and configurations because “if it ain’t broke, don’t fix it,” teams can ensure the integrity of updates before pushing them live. This allows them to take advantage of the latest software releases, close security gaps, and maintain compliance.
Meeting customer expectations for always-on digital services is a major challenge for any enterprise. That’s why it’s important for CIOs to empower their teams with hyperautomation and automate as many processes as possible. The network automation blueprint gives you the reference architecture that’s been validated by big tech as the safe way to build hyperautomated environments. This blueprint is now available just in time to help organizations prepare for the looming winter recession.
Get the Network Automation Blueprint now
Now is the time to prepare for winter, and you can start laying the groundwork for hyperautomation. Click the button below to download the network automation blueprint. You’ll see the same network architecture used by Big Tech, now tailored to help any size company provide reliable digital services.