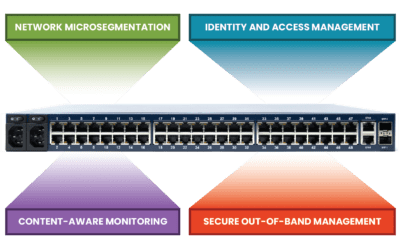
This post discusses the technologies that make up a zero trust gateway and explains how they work together to defend enterprise networks.
Month: April 2023
ZPE Systems’ Services Delivery Platform accelerates time-to-market
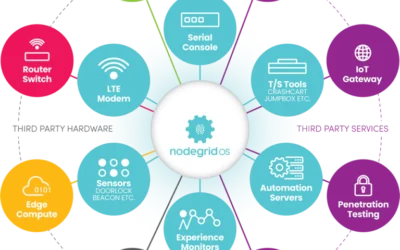
ZPE Systems’ Services Delivery Platform accelerates time-to-market with any app, anytime, anywhere IT teams can deliver instant business value with the on-demand services delivery architecture...
Zero Touch Deployment Cheat Sheet
This post provides a “cheat sheet” of solutions to the most common zero touch deployment challenges to help organizations streamline their automatic device provisioning.
ZPE Systems Partners with Atsign to Add Zero Attack Surface Technology
ZPE Systems has partnered with Atsign. Read the press release to learn more about zero attack surface technology.
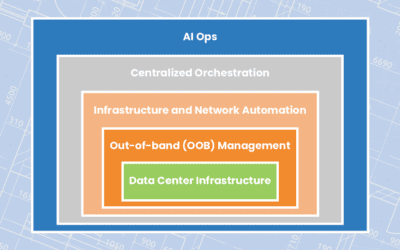
Streamlining Remote Data Center Management
Learn how to streamline remote data center management using technologies like OOB management, automation, orchestration, and AIOps to ensure network resiliency.
ZPE Systems keeps first responders mission-ready with FirstNet certification
ZPE Systems is now FirstNet certified. Read the press release here to see how we’re keeping first responders mission-ready.
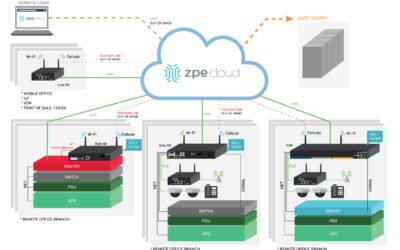
Cloud-Delivered Branch: Simplifying Remote Management
Describing the three cloud-based services involved in a cloud-delivered branch and illustrating how to implement a cloud-delivered branch with Nodegrid.
3 Gaps That Will Leave IT Teams Scrambling
Today’s IT teams must maintain a growing infrastructure of on-prem and cloud solutions. These range from physical routers, out-of-band devices, and firewalls, to Zero Trust Security solutions,...
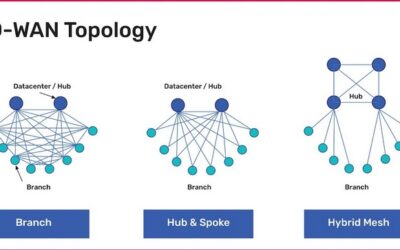
A Guide to SD-WAN Deployment Models
Learn about the most common SD-WAN deployment models with diagrams, pros and cons, and best practices to help organizations choose the right topology.