Organizations can protect their IT and Nvidia AI investments using the Core Edition console server and dual-CPU Jetson module.
Month: May 2024
DORA Compliance & Requirements
This guide outlines the technical requirements for DORA compliance and provides tips and best practices to streamline implementation.
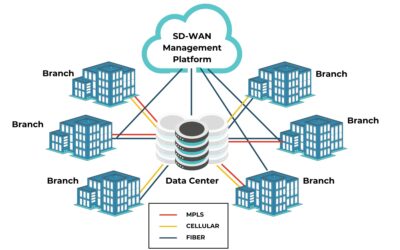
SD-WAN Management Guide
This SD-WAN management guide explains how this technology works, the potential benefits of using it, and the best practices to help you get the most out of your SD-WAN deployment.
PCI DSS 4.0 Requirements
This guide summarizes all twelve PCI DSS 4.0 requirements across six categories and describes the best practices for maintaining compliance.
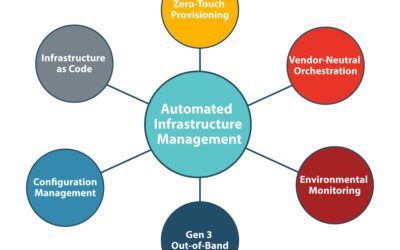
Automated Infrastructure Management for Network Resilience
A discussion of how automated infrastructure management improves network resilience by mitigating human error, accelerating recovery, and more.
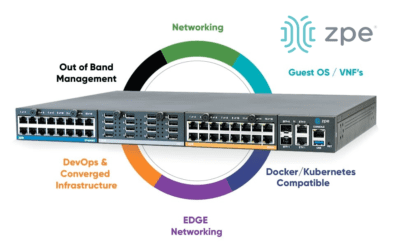
Cyberthreats are Soaring: ZPE Systems Urges Immediate Action with Gen 3 Console Servers to Thwart Breaches
Organizations using discontinued console servers can secure their infrastructure using ZPE’s new comprehensive solution. Get details here.
Cisco ISR 4431 EOL Replacement Guide
This guide compares Cisco ISR 4431 EOL replacement options and discusses the advanced features and capabilities offered by Cisco alternatives.