Automated Infrastructure Management for Network Resilience
Clients and end-users expect 24/7 access to digital services, but threats like ransomware and global political instability make it harder than ever to ensure continuous business operations. However, human error remains one of the biggest risks to business continuity, as illustrated by a misconfiguration that caused a recent McDonald’s outage. Despite the risk, many organizations must make do with lean IT teams and limited technology budgets, increasing the likelihood that an overworked engineer will make a mistake that brings down critical services.
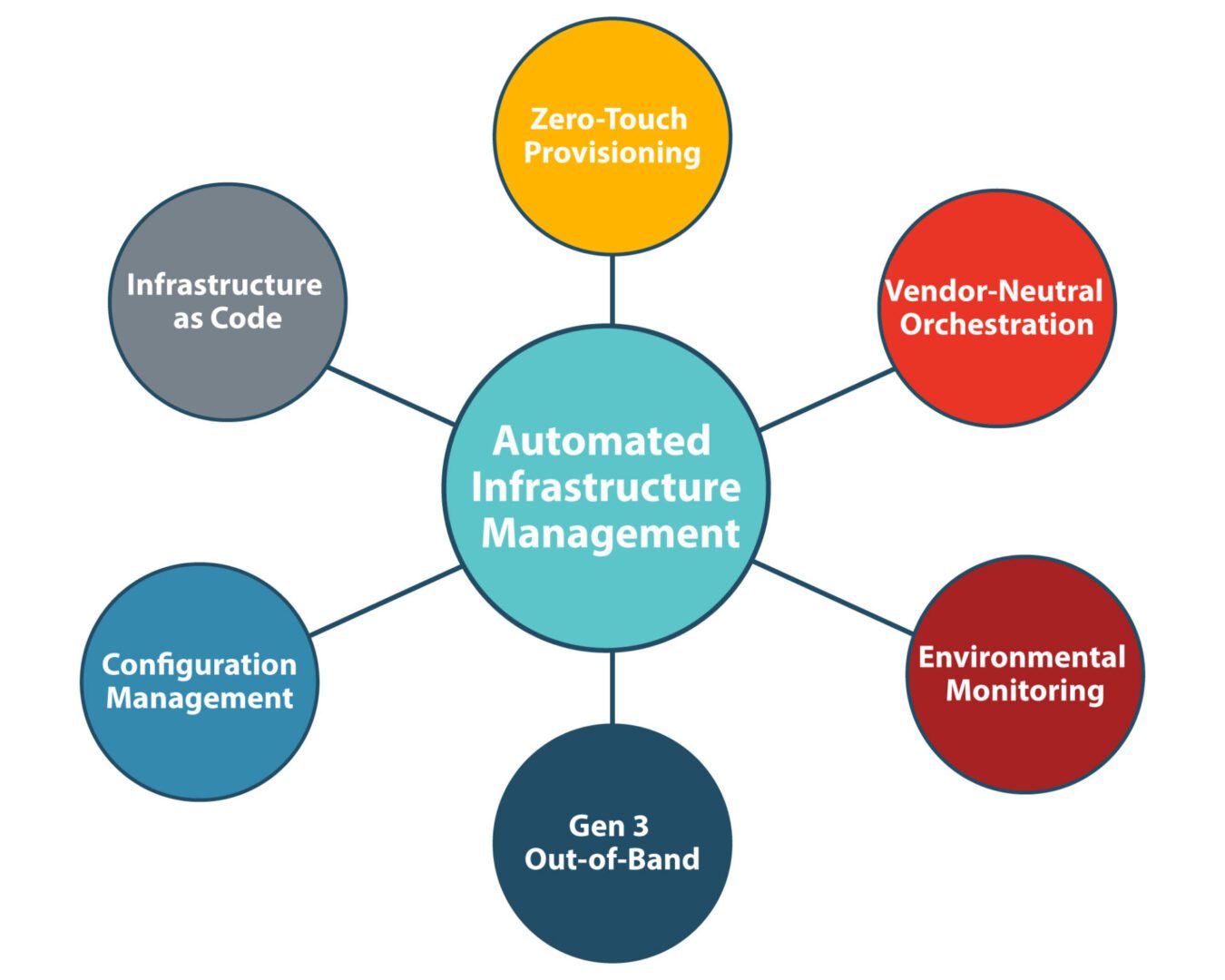
Automated infrastructure management reduces human intervention in workflows such as device configurations, software updates, and environmental monitoring. Automation improves network resilience by mitigating the risk of errors and making it easier to recover from failures.
How does infrastructure automation improve network resilience?
Network resilience is the ability to withstand or recover from adversity, service degradation, and complete outages with minimal business disruption. Automated infrastructure management improves resilience in three key ways:
- It reduces the risk of human error in configurations and updates,
- It catches environmental issues missed by human engineers, and
- It accelerates recovery by streamlining infrastructure rebuilds after failures and attacks
Let’s examine some of the infrastructure automation components and best practices that boost business resilience.
Zero-touch provisioning (ZTP)
Zero-touch provisioning (ZTP), also known as zero-touch deployment, uses software scripts or definition files to automatically configure new devices over the internet. ZTP allows teams to create and test a single configuration file, and then use it repeatedly to deploy new infrastructure. ZTP reduces the tediousness of new deployments, which in turn decreases the chances of errors. It also provides an opportunity to validate new configurations so any errors can be corrected before they’re deployed to production.
Infrastructure as Code (IaC)
Infrastructure as code (IaC) uses software abstraction to decouple infrastructure configurations from the underlying hardware. Similar to ZTP, IaC configurations are written as scripts or definition files, but they’re used to automatically provision virtual machines (VMs) and containers. Also like ZTP, IaC improves resilience by reducing human intervention in what is otherwise a tedious manual process. IaC also facilitates automatic configuration management.
Automatic configuration management
Automatic configuration management solutions continuously monitor in-place configurations to ensure they don’t drift away from documented standards. When necessary, they automatically install updates or roll back any unauthorized changes to prevent security vulnerabilities or configuration mistakes from bringing down the network.
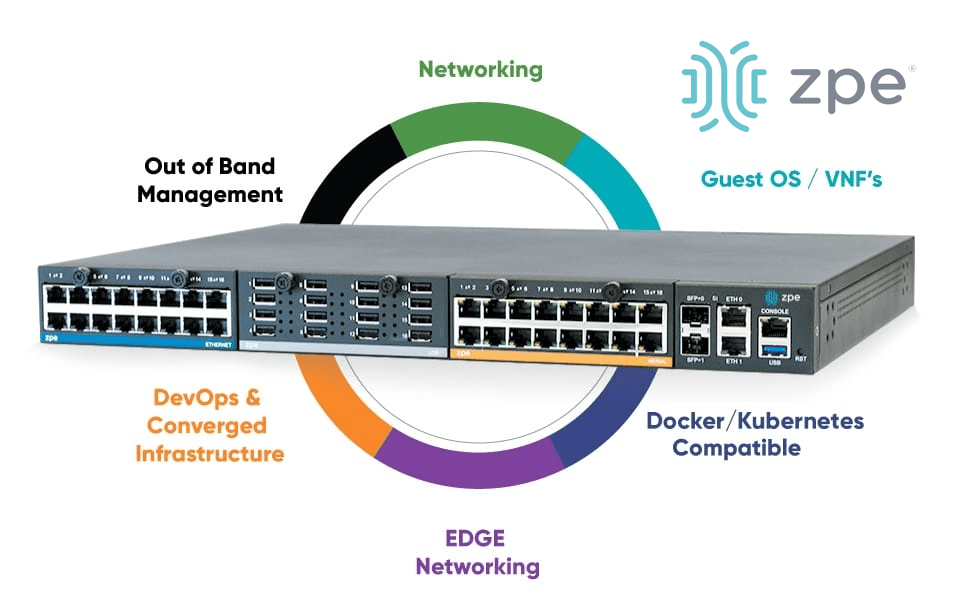
Gen 3 out-of-band (OOB) serial consoles
Out-of-band (OOB) serial consoles manage other infrastructure devices over a serial connection, separating the control plane from the data plane on a network dedicated to managing, troubleshooting, and orchestrating infrastructure. All OOB serial consoles improve network resilience by providing an alternative path to remote infrastructure that’s unaffected by issues on the production network. Gen 3 serial consoles go a step further by enabling vendor-neutral automation over the OOB connection. Gen 3 OOB serial consoles support third-party automation scripts and solutions and extend that automation to legacy and mixed-vendor infrastructure devices that are otherwise unsupported.
Additionally, Gen 3 OOB enables isolated management infrastructure (IMI), which prevents attackers on the production network from commandeering crown-jewel assets and vital business infrastructure. The OOB network also provides a safe environment where teams can recover from ransomware attacks without risking reinfection. Plus, a Gen 3 serial console can host all the tools teams need to automatically provision, test, and deploy new systems, accelerating recovery efforts for improved resilience.
Environmental monitoring
Environmental conditions like temperature, humidity, and air quality have a significant impact on the performance and lifespan of network infrastructure. That infrastructure is often housed in off-site data centers and branch offices, which means administrators may not know there’s an environmental concern until it’s already caused an error or outage. An environmental monitoring system uses sensors to collect data about conditions in remote facilities and automatically notify administrators of issues so they can respond before failures occur.
Vendor-neutral orchestration platforms
An automated network infrastructure comprises many moving parts and can be very complex to manage, especially if they don’t interoperate. Complexity increases the workload on IT staff that’s already stretched too thin, making mistakes more likely. A vendor-neutral orchestration platform unifies all the automation and management workflows behind a single pane of glass. Teams can use the automation tools they’re most comfortable with, decreasing errors while ensuring complete coverage of mixed-vendor and legacy infrastructure. Plus, using vendor-neutral management hardware like Nodegrid Gen 3 serial consoles allows teams to consolidate network functions, automation, security, and service hosting with a single device, further reducing complexity and boosting operational efficiency.
Automated infrastructure management is easier with Nodegrid
Infrastructure automation improves an organization’s ability to withstand and recover from adverse events by reducing human error, catching environmental issues before they cause outages, and accelerating recovery from ransomware and other failures. The Nodegrid platform from ZPE Systems provides Gen 3 out-of-band management, vendor-neutral hosting for automation and other third-party software, and unified orchestration for remote, mixed-vendor, and legacy infrastructure. Nodegrid simplifies automated infrastructure management for improved network resilience.
Ready to start your Automated Infrastructure Management for Network Resilience?
Learn more about boosting network resilience with automated infrastructure management by downloading ZPE’s Network Automation Blueprint.