This guide to collaboration in DevOps provides tips and best practices to bring Dev and Ops together while minimizing friction for maximum operational efficiency.
Increase Productivity
Terminal Servers: Uses, Benefits, and Examples
This guide answers all your questions about terminal servers, discussing their uses and benefits before describing what to look for in the best terminal server solution.
What is a Hyperscale Data Center?
This blog defines a hyperscale data center deployment before discussing the unique challenges involved in managing and supporting such an architecture.
Healthcare Network Design
A guide to resilient healthcare network design using technologies like automation, edge computing, and isolated recovery environments (IREs).
Best DevOps Tools
This blog discusses the various workflows involved in the DevOps lifecycle that can be automated with the best DevOps tools.
Best Network Performance Monitoring Tools
This guide compares three of the best network performance monitoring tools by analyzing the most critical factors and discussing the pros and cons.
Breaking Down The 2023 Ragnar Locker Cyberattacks
Many organizations suffered Ragnar Locker cyberattacks in 2023. 30-year cybersecurity expert James Cabe discusses the problem and solution.
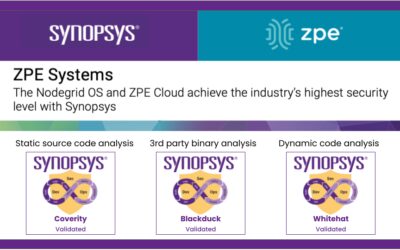
Nodegrid OS and ZPE Cloud achieve industry’s highest security with Synopsys
ZPE Systems achieves the industry’s highest security level by incorporating Synopsys code-quality measures. Read the details here.
OOB Network Management Software Tools
Comparing the four best OOB network management software tools and discussing the features, pros, and cons to help you make the best choice for your environment.
Living Spaces Furniture: Scaling to 50 sites with only 3 network staff
Download the case study to see how Living Spaces cut costs by $300,000 per year and scaled across the U.S. with only 3 network staff.