Best DevOps Tools
The best DevOps tools
DevOps version control
In a DevOps environment, a whole team of developers may work on the same code base simultaneously for maximum efficiency. DevOps version control tools like GitHub allow you to track and manage all the changes made to a code base, providing visibility into who’s making what changes at what time. Version control prevents devs from overwriting each other’s work or making unauthorized changes. For example, a developer may come up with a way to improve the performance of a feature by changing the existing code, but doing so inadvertently creates a vulnerability in the software or interferes with other application functions. DevOps version control prevents unauthorized code changes from integrating with the rest of source code and tracks who’s responsible for making the request, improving the stability and security of the software.
- Best DevOps version control tool: Github
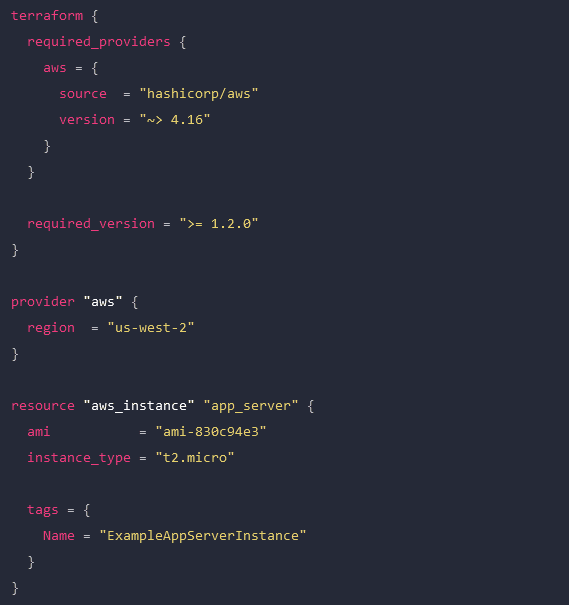
Infrastructure as Code (IaC)
Infrastructure as Code (IaC) streamlines the Operations side of a DevOps environment by abstracting server, VM, and container configurations as software code. IaC build tools like HashiCorp Terraform allow Ops teams to write infrastructure configurations as declarative or imperative code, which is used to provision resources automatically. With IaC, teams can deploy infrastructure at the velocity required by DevOps development cycles.
An example Terraform configuration for IaC.
- Best Infrastructure as Code (IaC) tool: HashiCorp Terraform
Configuration management
Configuration management involves monitoring infrastructure and network devices to make sure no unauthorized changes are made while systems are in production. Unmonitored changes could introduce security vulnerabilities that the organization is unaware of, especially in a fast-paced DevOps environment. In addition, as systems are patched and updated over time, configuration drift becomes a concern, leading to additional quality and security issues. DevOps configuration management tools like RedHat Ansible automatically monitor configurations and roll back unauthorized modifications. Some IaC build tools, like Terraform, also include configuration management.
- Best configuration management tool: RedHat Ansible
Continuous Integration/Continuous Delivery (CI/CD)
Continuous Integration/Continuous Delivery (CI/CD) is a software development methodology that goes hand-in-hand with DevOps. In CI/CD, software code is continuously updated and integrated with the main code base, allowing a continuous delivery of new features and improvements. CI/CD tools like Jenkins automate every step of the CI/CD process, including software building, testing, integrating, and deployment. This allows DevOps organizations to continuously innovate and optimize their products to stay competitive in the market.
- Best CI/CD tool: Jenkins
Software testing
Not all DevOps teams utilize CI/CD, and even those that do may have additional software testing needs that aren’t addressed by their CI/CD platform. In DevOps, app development is broken up into short sprints so manageable chunks of code can be tested and integrated as quickly as possible. Manual testing is slow and tedious, introducing delays that prevent teams from achieving the rapid delivery schedules required by DevOps organizations. DevOps software testing tools like Selenium automatically validate software to streamline the process and allow testing to occur early and often in the development cycle. That means high-quality apps and features get out to customers sooner, improving the ROI of software projects.
- Best software testing tool: Selenium
Container management
In DevOps, containers are lightweight, virtualized resources used in the development of microservice applications. Microservice applications are extremely agile, breaking up software into individual services that can be developed, deployed, managed, and destroyed without affecting other parts of the app. Docker is the de facto standard for basic container creation and management. Kubernetes takes things a step further by automating the orchestration of large-scale container deployments to enable an extremely efficient and streamlined infrastructure.
- Best container management tools: Docker and Kubernetes
Monitoring & incident management
Continuous improvement is a core tenet of the DevOps methodology. Software and infrastructure must be monitored so potential issues can be resolved before they affect software performance or availability. Additionally, monitoring data should be analyzed for opportunities to improve the quality, speed, and usability of applications and systems. DevOps monitoring and incident response tools like Cisco’s AppDynamics provide full-stack visibility, automatic alerts, automated incident response and remediation, and in-depth analysis so DevOps teams can make data-driven decisions to improve their products.
- Best monitoring & incident management tool: Cisco AppDynamics
Deploy the best DevOps tools with Nodegrid
DevOps is all about agility, speed, and efficiency. The best DevOps tools use automation to streamline key workflows so teams can deliver high-quality software faster. With so many individual tools to manage, there’s a real risk of DevOps tech sprawl driving costs up and inhibiting efficiency. One of the best ways to reduce tech sprawl (without giving up all the tools you love) is by using vendor-neutral platforms to consolidate your solutions. For example, the Nodegrid Services Delivery Platform from ZPE Systems can host and integrate 3rd-party DevOps tools, reducing the need to deploy additional virtual or hardware resources for each solution. Nodegrid utilizes integrated services routers, such as the Gate SR or Net SR, to provide branch/edge gateway routing, in-band networking, out-of-band (OOB) management, cellular failover, and more. With a Nodegrid SR, you can combine all your network functions and DevOps tools into a single integrated solution, consolidating your tech stack and streamlining operations.
A major benefit of using Nodegrid is that the Linux-based Nodegrid OS is Synopsys secure, meaning every line of source code is checked during our SDLC. This significantly reduces CVEs and other vulnerabilities that are likely present in other vendors’ software.
Learn more about efficient DevOps management with vendor-neutral solutions
With the vendor-neutral Nodegrid Services Delivery Platform, you can deploy the best DevOps tools while reducing tech sprawl. Watch a free Nodegrid demo to learn more.