Casino giants in the US were hit by ransomware in September 2023. Cyber expert James Cabe breaks down the attack & how to recover.
Jordan Baker
The Biggest Ransomware Attack You Haven’t Heard of…Yet
The most successful ransomware attack ever is happening right now. See why isolated management infrastructure is the only way to save your organization.
Atsign: Why Choose ZPE Systems to Host IoT Security?
In this guest post, Atsign CTO & Co-Founder Colin Constable discusses how their IoT security solutions just work with ZPE Systems.
Out-of-Band Recovery Kit – ZPE Systems at Cisco Live 2023
Koroush Saraf shows off ZPE’s Out-of-Band Recovery Kit that lets engineers instantly recover from SD-WAN outages and critical downtime.
99.999% Uptime for a Top-10 Engineering School
From data center to edge, see how Nodegrid Services Routers saved hundreds of hours per month for an engineering school’s IT team.
Putting Operations on Autopilot – ZPE Presents at Cisco Live 2023
Jennifer Autry presents the story of Vapor IO. See how they used automation to reduce deployment times and make operations more efficient.
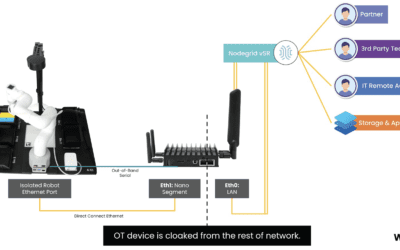
How to remove IoT & OT from your attack surface
Summary With IoT and OT (operationalized technology) sprawling across the globe, organizations are able to provide more value to their customers. But for IT security teams, this presents a growing...
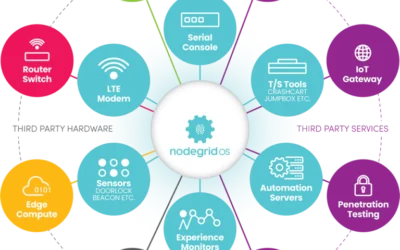
ZPE Systems’ Services Delivery Platform accelerates time-to-market
ZPE Systems’ Services Delivery Platform accelerates time-to-market with any app, anytime, anywhere IT teams can deliver instant business value with the on-demand services delivery architecture...
ZPE Systems Partners with Atsign to Add Zero Attack Surface Technology
ZPE Systems has partnered with Atsign. Read the press release to learn more about zero attack surface technology.
ZPE Systems keeps first responders mission-ready with FirstNet certification
ZPE Systems is now FirstNet certified. Read the press release here to see how we’re keeping first responders mission-ready.