Mike Sale discusses why Gen 3 out-of-band management is a strategic weapon that helps you get better ROI on your IT investments.


Mike Sale discusses why Gen 3 out-of-band management is a strategic weapon that helps you get better ROI on your IT investments.

AI system reliability is about ensuring AI is available even when things go wrong. Here’s why secure remote network management is key.
Organizations are rethinking their cloud strategy. Our article covers why a hybrid cloud approach can maximize efficiency and control.
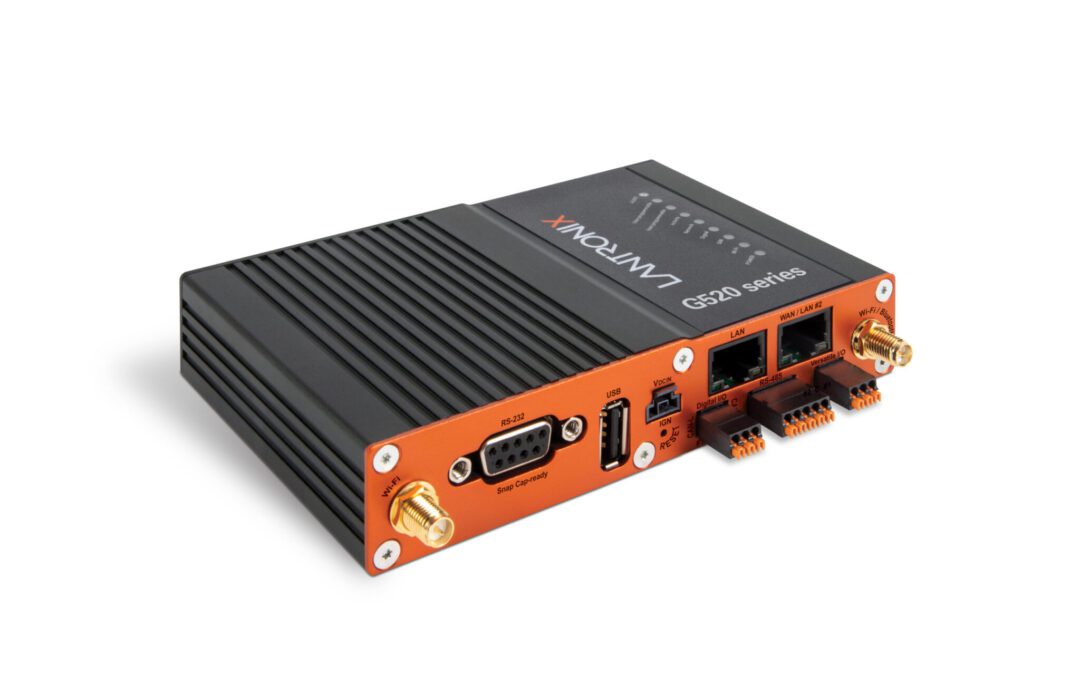
Discussing where the G520 falls short, why it matters, and alternative options that deliver consolidated IIoT capabilities and network resilience.
Read our post for the latest insights about edge computing from Gartner. We cover edge computing platforms and how to address the challenges.

Starlink is a high-speed alternative to POTS lines, and offers plenty of flexibility when cellular coverage is lacking. Here’s our setup guide.

Passive optical networking (PON) is a high-speed broadband technology that enables the delivery of multiple services over a single fiber optic cable.
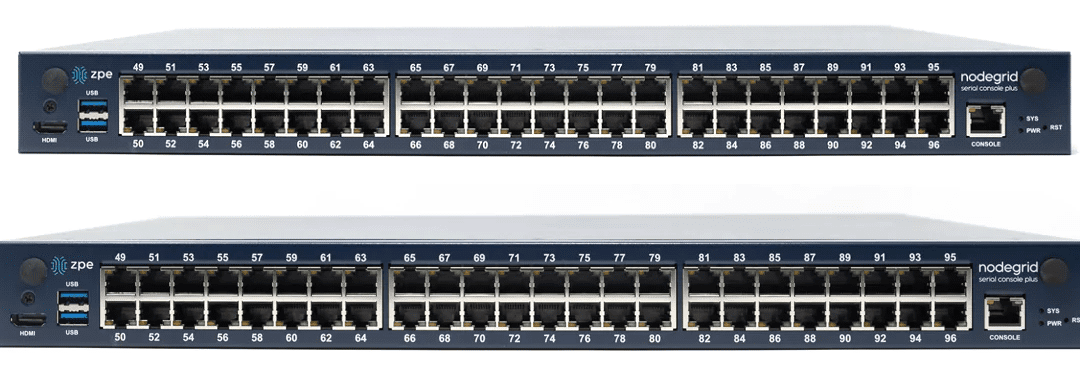
Console server hardware can vary significantly across different vendors and use cases. Learn how to find the right solution for your deployment.

This blog describes various methods for achieving data center scalability before providing tips and best practices to make scalability easier and more cost-effective to implement.

This guide compares the most popular edge security solutions and offers recommendations for choosing the right vendor for your use case.

This blog discusses some of the applications of edge computing for industries like finance, retail, and manufacturing and provides advice on how to get started.
This blog highlights 7 edge computing examples from across many different industries and provides tips and best practices for each use case.

This guide compares edge computing vs cloud computing to help organizations choose the right deployment model for their use case.
This edge computing architecture guide provides information and resources needed to ensure a streamlined, resilient, and cost-effective deployment.

This guide describes the 10 minimum cybersecurity requirements mandated by NIS2 and provides tips to simplify NIS2 compliance.

This guide outlines the technical requirements for DORA compliance and provides tips and best practices to streamline implementation.
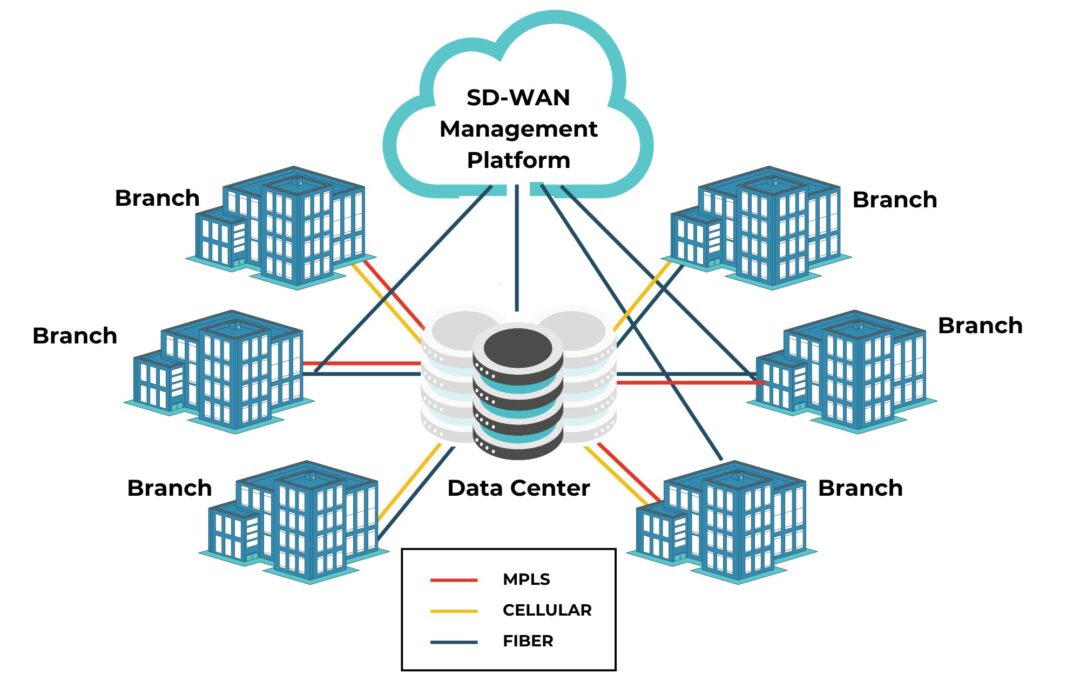
This SD-WAN management guide explains how this technology works, the potential benefits of using it, and the best practices to help you get the most out of your SD-WAN deployment.

This guide summarizes all twelve PCI DSS 4.0 requirements across six categories and describes the best practices for maintaining compliance.
The Digital Operational Resilience Act (DORA Act) outlines significant resilience changes for the financial sector. See how to comply here.

Explaining the challenges that make ISP network architectures less resilient and providing solutions for overcoming these hurdles.

This post describes some of the most common Intel NUC use cases, explains the security and management issues that caused its discontinuation, and provides superior replacement options.
From data center to edge, see how Nodegrid Services Routers saved hundreds of hours per month for an engineering school’s IT team.

In this guide, we’ll compare migration options for the Cisco ISR 2900 EOL models to help you select a solution that suits your business use case, deployment size, and future growth.
Software-defined wide area networking, or SD-WAN, has made it possible to efficiently control highly distributed WAN architectures using software abstraction and automation. SD-WAN adoption is increasing, partially due to the rise in remote work during the pandemic,...

What is hybrid cloud infrastructure, and how is it achieved? Comparing the expectations vs. reality of hybrid cloud with solutions to common problems.

The Gen 3 serial console is the latest innovation in out-of-band management.But what exactly is it, and where did it come from? In this post, we’ll briefly cover the basics of serial consoles and why you need them, and then dive into the evolving needs that brought...

Watch agile networking in action with these Nodegrid demos ZPE® Systems Network Solutions Architect Rene Neumann shows you how easy it is to enable agile networking. See Nodegrid and ZPE Cloud first hand with our collection of demo videos. You'll learn how to:...
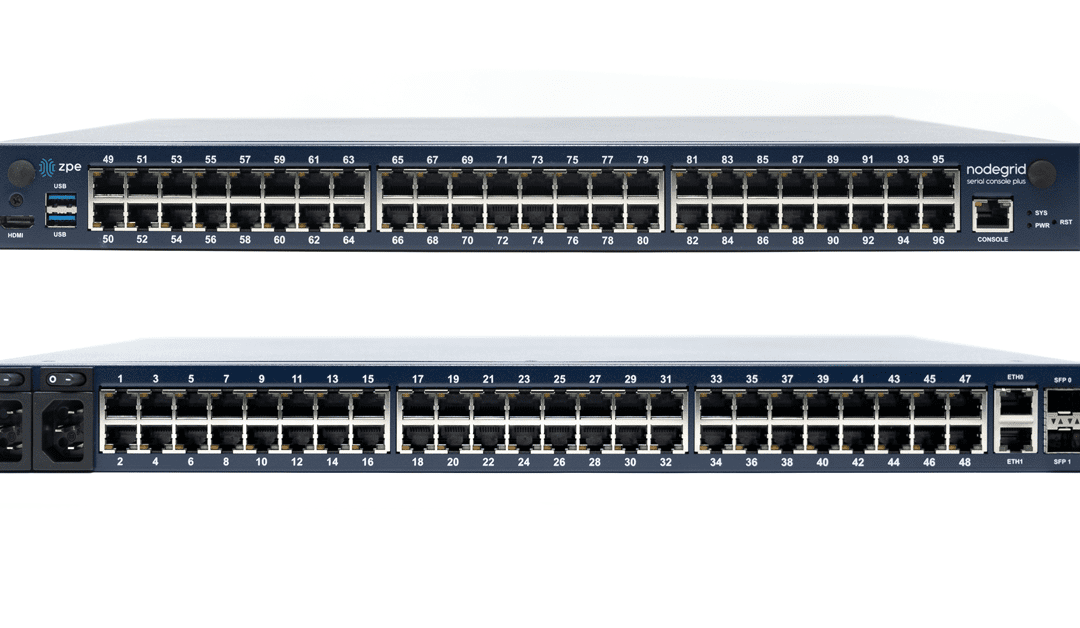
Fremont, CA, June 22, 2021 – ZPE Systems adds to their lineup of datacenter infrastructure management solutions with the Nodegrid Serial Console Plus (NSCP). Like previous generations of Nodegrid Serial Console, the NSCP is a high-density appliance that streamlines...
Fremont, CA, March 31, 2021 – ZPE Systems, Inc., a leading innovator of network devices and cloud-based infrastructure management solutions trusted by the world’s top companies, officially launched the Edge Transformation Partner Program. This program is designed for...
We’re entering the era of edge networking Edge networking is critical to the future. Organizations continue to expand, and analysts predict that the data center won’t be the only workhorse when it comes to enterprise networking. In fact, some estimate that in a couple...

In the finance industry, network modernization protects the most confidential customer data. Whether for processing minor withdrawals & deposits, or recording asset transactions & real estate purchases, your network must be secure and reliable from the ground...

When your car needs new tires, or some other repair, (AND YOU KNOW IT) do you wait until you get a flat on the freeway, or break down and need a tow? Or do you (PROACTIVELY) take it to the shop for new tires or repairs before something happens that ends up costing you...